'ANNOUNCE: SpamAssassin 3.1.0 available!' - MARC
Phew. That took a while, but it's worth it ;)
(Things I found interesting recently.)
'ANNOUNCE: SpamAssassin 3.1.0 available!' - MARC
Phew. That took a while, but it's worth it ;)
Do you use anti-spam DNS blocklists? If so, you should probably go take a look at DnsblAccuracy082005 on the SpamAssassin wiki; I've collated the results from our recent mass-check rescoring runs for 3.1.0, to produce have up-to-date measurements of the accuracy and hit-rates for most of the big DNS blocklists.
A few highlights:
We don't have accurate figures for the new URIBL.COM lists, btw -- only the rulesets that are distributed with SpamAssassin were measured.
I get quite a lot of spam. For one random day last month (Aug 21st), I got 48 low-scoring spam mails (between 5 and 10 points according to SpamAssassin), and 955 high-scorers (anything over 10). I don't know how much malware I get, since my virus filter blocks them outright, instead of delivering to a folder.
That's all well and good, because spam and viruses are now relatively easy to filter -- and if I recall correctly, they were all correctly filed, no FPs or FNs (well, I'm not sure about the malware, but fingers crossed ;).
The hard part is now 'bogus bounces' -- the bounces from 'good' mail systems, responding to the forged use of my addresses as the sender of malware/spam mails. There were 306 of those, that day.
Bogus bounces are hard to filter as spam, because they're not spam -- they're 'bad' traffic originating from 'good', but misguided, email systems. They're not malware, either. They're a whole new category of abusive mail traffic.
I say 'misguided', because a well-designed mail system shouldn't produce these. By only performing bounce rejection with a 4xx or 5xx response as part of the SMTP transaction, when the TCP/IP connection is open between the originator and the receiving MX MTA, you avoid most of the danger of 'spamming' a forged sender address. However, many mail systems were designed before spammers and malware writers started forging on a massive scale, and therefore haven't fixed this yet.
I've been filtering these for a while using this SpamAssassin ruleset; it works reasonably well at filtering bounces in general, catching almost all of the bounces. (There is a downside, though, which is that it catches more than just bogus bounces -- it also catches real bounces, those in response to mails I sent. At this stage, though, I consider that to be functionality I'm willing to lose.)
The big remaining problem is challenge-response messages.
C-R is initially attractive. If you install it, your spam load will dwindle to zero (or virtually zero) immediately -- it'll appear to be working great. What you won't see, however, is what's happening behind the scenes:
your legitimate correspondents are getting challenges, will become annoyed (or confused), and may be unwilling or unable to get themselves whitelisted;
spam that fakes other, innocent third party addresses as the sender, will be causing C-R challenges to be sent to innocent, uninvolved parties.
The latter is the killer. In effect, you're creating spam, as part of your attempts to reduce your own spam load. C-R shifts the cost of spam-filtering from the recipient and their systems, to pretty much everyone else, and generates spam in the process. I'm not alone in this opinion.
That's all just background -- just establishing that we already know that C-R is abusive. But now, it's time for the next step for me -- I've had enough.
I initially didn't mind the bogus-bounce C-R challenges too much, but the levels have increased. Each day, I'm now getting a good 10 or so C-R challenges in response to mails I didn't send. Worse, these are the ones that get past the SpamAssassin ruleset I've written to block them, since they don't include an easy-to-filter signature signifying that they're C-R messages, such as Earthlink's 'spamblocker-challenge' SMTP sender address or UOL's 'AntiSpam UOL' From address. There seems to be hundreds of half-assed homegrown C-R filters out there!
So now, when I get challenge-response messages in response to spam which forges one of my addresses as the 'From' address, and it doesn't get blocked by the ruleset, I'm going to jump through their hoops so the spam is delivered to the C-R-protected recipient. Consider it a form of protest; creating spam, in order to keep youself spam-free, is simply not acceptable, and I've had enough.
And if you're using one of these C-R filters -- get a real spam filter. Sure they cost a bit of CPU time -- but they work, without pestering innocent third parties in the process.
Yes, I've been growing a beard. Strangely, it seems to be going quite well! Here's a good pic of beardy Justin, standing on a bridge over the Merced river in Yosemite:
Lots more pics from the holiday should be appearing here shortly, if you're curious.
Well, I'm back... it appears that Google Maps link I posted wasn't too much use in deciphering where I was going; sorry about that. Myself and C spent a fun week and a bit, driving up to Kings Canyon and Yosemite, backpacking around for a few days, then driving back down via the 395 via Bishop, Mammoth Lakes, Lone Pine and so on.
Kings Canyon: Unfortunately, not so much fun; we had the bad luck of encountering what must be the tail end of the mosquito season, and spent most of our 2 days there running up and down the Woods Creek trail without a break, entirely surrounded by clouds of mozzies. Possibly this headlong dashing explains how we ran into so much other wildlife -- including a (harmless) California Mountain King Snake and, less enjoyably -- and despite wearing bear bells on our packs to avoid this -- a black bear...
We rounded a corner on the trail, and there it was, munching on elderberries. Once we all spotted each other, there were some audible sounds of surprise from both bear and humans, and the bear ran off in the opposite direction; the humans, however, did not. We were about 500 feet from our camp for the night, so we needed to get past where the bear had been, or face a long walk back.
Despite some fear (hey, this was our first bear encounter!), we stuck around, shouted, waved things, and took the various actions you take. It all went smoothly, the bear had probably long since departed, but we took it slow regardless, and had a very jittery night in our tent afterwards. After that, and the unceasing mozzie onslaught, we were in little hurry to carry on around the planned loop, so we cut short our Kings Canyon trip by a day and just returned down the trail to its base.
Yosemite: a much more successful trip. There were many reasons, primarily that the mosquito population was much, much lower, and discovering that the Tuolumne Meadows Lodge -- comfortable tent cabins, excellent food, and fantastic company -- provided a truly excellent base camp.
But I'd have to say that the incredible beauty of Tuolumne Meadows and the Vogelsang Pass really blew me away. I don't think I've seen any landscape quite like that, since trekking to Annapurna Base Camp in Nepal. I'm with John Muir -- Yosemite and its surrounds are a wonder of the world.
Lee Vining: had to pick up a sarnie at the world-famous Whoa Nellie Deli. Yum! After all the camping, we stayed in a hotel with TV, got some washing done, and watched scenes from a J.G. Ballard novel play out on NBC and CNN. Mind-boggling.
Mammoth Lakes: A quick kvetch. Mammoth is possibly the most pedestrian-hostile town I've ever visited. They have a hilarious section of 100 feet of sidewalk, where I encountered a fellow pedestrian using those ski-pole-style hiking walking sticks, and entirely in seriousness. Was the concept of walking so foreign in that town that long-distance walking accessories were required? I don't know, but it didn't make up for the other 90% of the streets where peds were shoved off onto the shoulder, in full-on 'sidewalk users aren't welcome here' Orange County style.
On top of that, the single pedestrian crossing in the main street spans five lanes of traffic, with no lighting, warning signs, or indeed any effective way for drivers to know whether peds were crossing or not. Unsurprisingly we nearly got run over when we tried using the damn thing. Best avoided.
I'm amazed -- it's like they designed the town to be ped-hostile. Surely allowing peds to get around your town is a bonus when you're a ski resort for half of the year? Meh.
Anyway, back again, a little refreshed. Once more into the fray...
I'm taking a week off to go hiking in some of the amazing back country that California has to offer. Assuming I don't get eaten by a bear, I'll see you all around Sep 6....
An interesting technique, from the ClamAV development list -- using Bloom filters to speed up string searching. This kind of thing works well when you've got 1 input stream, and a multitude of simple patterns that you want to match against the stream. Bloom filters are a hashing-based technique to perform extremely fast and memory-efficient, but false-positive-prone, binary lookups.
The mailing list posting ('Faster string search alternative to Boyer-Moore') gives some benchmarks from the developers' testing, along with the core (GPL-licensed) code:
Regular signatures (28,326) :
Extended Boyer-Moore: 11 MB/s
BloomAV 1-byte: 89 MB/s
BloomAV 4-bytes: 122 MB/s
Some implementation details:
the (implementation) we chose is a simple bit array of (256 K * 8) bits. The filter is at first initialized to all zeros. Then, for every virus signature we load, we take the first 7 bytes, and hash it with four very fast hash functions. The corresponding four bits in the bloom filter are set to 1s.
Our intuition is that if the filter is small enough to fit in the CPU cache, we should be able to avoid memory accesses that cost around 200 CPU cycles each.
Also, in followup discussion, the following paper was mentioned: A paper describing hardware-level Bloom filters in the Snort IDS -- S. Dharmapurikar, P. Krishnamurthy, T. Sproull, and J. W. Lockwood, "Deep packet inspection using parallel Bloom filters," in Hot Interconnects, (Stanford, CA), pp. 44--51, Aug. 2003.
This system is dubbed 'BloomAV'. Pretty cool. It's unclear if the ClamAV developers were keen to incorporate it, though, but it does point at interesting new techniques for spam signatures.
Bluetooth As a Laptop Sensor in Cambridge, England.
I link-blogged this yesterday, where it got picked up by Waxy, and thence to Boing Boing -- where some readers are reportedly considering it doubtful. Craig also expressed some skepticism. However, I think it's for real.
Check out the comments section of Schneier's post -- there's a few notable points:
Some Bluetooth-equipped laptops will indeed wake from suspend to respond to BT signals.
Davi Ottenheimer reports that the current Bluetooth spec offers "always-on discoverability" as a feature. (Obviously the protocol designers let usability triumph over security on that count.)
Many cellphones are equipped with Bluetooth, and can therefore be used to detect other 'discoverable' BT devices in range.
Walking around a UK hotel car park, while pressing buttons on a mobile phone, would be likely to appear innocuous -- I know I've done it myself on several occasions. ;)
Finally -- this isn't the first time the problem has been noted. The same problem was reported at Disney World, in the US:
Here's the interesting part: every break-in in the past month (in the Disney parking lots) had involved a laptop with internal bluetooth. Apparently if you just suspend the laptop the bluetooth device will still acknowledge certain requests, allowing the thief to target only cars containing these laptops.
Mind you, perhaps this is a 'chinese whispers' case of the Disney World thefts being amplified. Perhaps it was noted as happening in Disney World, reported in an 'emerging threats' forum where the Cambridgeshire cop heard it, and he then picked it up as something worth warning the public about, without knowing for sure that it was happening locally.
Update: aha. An observant commenter on Bruce Schneier's post has hit on a possibly good reason why laptops implement wake-on-Bluetooth:
On my PowerBook, the default Bluetooth settings were "Discoverable" and "Wake-on-Bluetooth" -- the latter so that a Bluetooth keyboard or mouse can wake the computer up after it has gone to sleep.
Emergent Chaos: I'm a Spamateur:
In private email to Justin "SpamAssassin" Mason, I commented about blog spam and "how to fix it," then realized that my comments were really dumb. In realizing my stupidity, I termed the word "spamateur," which is henceforth defined as someone inexperienced enough to think that any simple solution has a hope of fixing the problem.
I think this is my new favourite spam neologism ;)
Environment: Kung Fu Monkey: Hybrids and Hypotheses. A great discussion of the Toyota Prius:
Kevin Drum recently quoted a study which re-iterated that there's no "real" advantage to buying a hybrid. It's only just as convenient -- so if you're driving a hybrid, you're doing it for some other reason than financial incentive.
That made me think: what a perfect example of just how fucking useless as a society we've become. We can't even bring ourselves to do the right thing when it's only JUST as convenient as doing the wrong thing. And that's not even considered odd. Even sadder.
It's the kind of plot twist that will send some critics screaming into the aisles: Why not let writers patent their screenplay ideas? The U.S. Patent and Trademark Office already approves patents for software, business methods -- remember Amazon.com's patent on 'one-click' Internet orders? -- even role-playing games. So why not let writers patent the intricate plot of the next cyberthriller?
So in other words, a law grad called Andrew Knight actually wants to see the world RMS described in his 'Patent Absurdity' article for the Guardian, where Les Miserables was unpublishable due to patent infringement. Incredible.
He himself plays the classic lines, familiar to those who followed the EU software patenting debate:
Knight agrees, up to a point. He won't reveal the exact details of the plots he's submitted to the Patent Office, other than to say they involve cyberspace. And he says patents would apply only to ideas that are unique and complex. But he worries that without patent protection, some Hollywood sharpies could change ideas like his around and pass them off as their own.
''I'm trying to address a person who comes up with a brand-new form of entertainment who may not be a Poe, may not be a Shakespeare, but still deserves to be paid for his work,'' Knight says. ''Otherwise, who will create anything?''
A perfect pro-patent hat trick!
Linux: PingWales' round-up of UKUUG Linux 2005 Day 3 includes this snippet:
As well as running (Virtual Machines), Xen allows them to be migrated on the fly. If a physical system is overloaded, or showing signs of failure, a virtual machine can be migrated to a spare node. This process takes time, but causes very little interruption to service. The machine state is first copied in its entirety, then the changes are copied repeatedly until there are a small enough number than the machine can be stopped, the remaining changes copied and the new version started. This usually provides a service interruption of under 100ms - a small enough jitter that people playing Quake 3 on a server in a virtual machine did not notice when it was moved to a different node.
Now that is cool.
Images: Jim Winstead's walk up Broadway from a few days ago has already garnered a few interested parties, since he's Creative-Commons-licensed all the photos, and they're easily findable via Google and on Flickr.
I find this interesting; the collision between open source, photography and cartography is cool. The result is a version of maps.A9.com, where you can actually use the images legally in your own work. More people should do this for other cities.
Spam: during a recent discussion on the SpamAssassin dev list, the question came up as to how long a rule could expect to maintain its effectiveness once it was public -- the rule secrecy issue.
In order to make a point -- that certain types of very successful rules can indeed last a long time -- I picked out one rule, MIME_BOUND_DD_DIGITS. Here's a smartened-up copy of what I found out.
This rule matches a certain format of MIME boundary, one observed in 17.4637% of our spam collection and with 0 nonspam hits. Since we have a massive collection of mails, received between Jan 2004 to May 2005, and a rule with a known history, we can then graph its effectiveness over time.
The rule's history was:
So, we would expect to see a drop in its effectiveness against spam in late May 2004 and onwards, if the spammers were reacting to SVN changes; or post September 2004, if they react to what's released.
By graphing the number of hits on mails within each 2-hour window, we can get a good idea of its effectiveness over time:
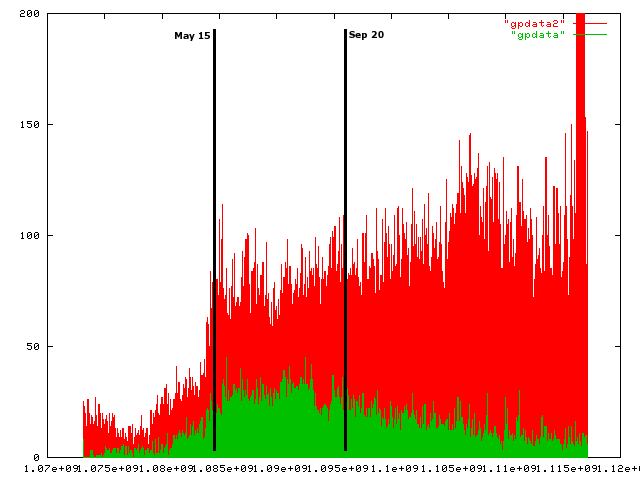
The red bars are total spam mails in each time period; green bars, the number of spam mails that hit the rule in each period. May 15 2004 and Sep 20 2004 are marked; Jan 2004 is at the left, and May 2005 is at the right-most extreme of the graph. (There's a massive spike in spam volume at the right -- I think this is Sober.Q output, which disappears after a week or so.)
It appears that the rule remains about even in effectiveness in the 4 months it's in SVN, but unreleased; it declines a little more after it makes it into a SpamAssassin release. However, it trails off very slowly -- even in May 2005, it's still hitting a good portion of spam.
Given this, I suspect that most spammers are not changing structural aspects of their spam in response to SpamAssassin with any particular alacrity, or at least are not capable of doing so.
To speculate on the latter, I think many spammers are using pirated copies of the spamware apps, so cannot get their hands on updated versions through 'legitimate' channels.
Speculating on the former -- in my opinion there's a very good chance that SpamAssassin just isn't a particular big target for them to evade, compared to the juicy pool of gullible targets behind AOL's filters, for example. ;)
Ireland: There's been some discussion about 'an Irish EFF' recently, reminding me of the old days of Electronic Frontier Ireland in the 1990s.
I was reminded of this by Danny O'Brien's article in The Guardian, where he notes an interesting point -- half of the effectiveness of the EFF in the US, is because they have a few full-time people sitting in an office, answering phone calls. Essentially they act as a human PBX, being the go-to guy connecting journalists to activists and experts.
Now that is something that could really work, and is needed in Ireland, which is in the same boat as the UK in this respect; the journalists don't know who to ask for a reliable opposing opinion when the BSA, ICT Ireland, or the IRMA put out incorrect statements. It has to be someone who's always available for a quote at the drop of a hat, over the phone. From experience, this takes dedication -- and without getting paid for it, it's hard to keep the motivation going.
IrelandOffline have done it pretty well for the telecoms issue; ICTE have done a brilliant job, the best I've seen in Europe IMO, of grabbing hold of the e-voting issue to the stage where they own it; but for online privacy, software patenting, and other high-tech-meets-society issues, there's nobody doing it that successfully.
(Update: added ICTE, slipped my mind! Sorry Colm!)
Tech: One of the first online periodicals I started reading regularly, when I first got access to USENET back in 1989 or so, was comp.risks -- Peter G. Neumann's RISKS Forum. Since then, I've been reading it religiously, in various formats over the years.
It appears that RISKS has just celebrated its 20th anniversary.
Every couple of weeks it provides a hefty dose of computing reality to counter the dreams of architecture astronauts and the more tech-worshipping members of our society, who fail to realise that just because something uses high technology, doesn't necessarily make it safer.
I got to meet PGN a couple of weeks ago at CEAS, and I was happy to be able to give my thanks -- RISKS has been very influential on my code and my outlook on computing and technology.
Nowadays, with remote code execution exploits for e-voting machines floating about, and National Cyber-Security Czars, I'd say RISKS is needed more than ever. Long may it continue!
Words: 'Pharming'. I recently came across this line in a discussion document:
'Wait, isn't this exactly the kind of attack pharmers mount?'
I was under the impression that 'pharming' was a transgenics
term: 'In pharming, ... genetically modified (transgenic) animals are
mostly used to make human proteins that have medicinal value. The protein
encoded by the transgene is secreted into the animal's milk, eggs or
blood, and then collected and purified. Livestock such as cattle, sheep,
goats, chickens, rabbits and pigs have already been modified in this way
to produce several useful proteins and drugs.'
Obviously this wasn't what was being referred to. So I got googling. It appears the sales and marketing community of various security/filtering/etc. companies, have been getting all het up about various phishing-related dangers.
The earliest article I could find was this -- GCN: Is a new ID theft scam in the wings? (2005-01-14):
''Pharming is a next-generation phishing attack,' said Scott Chasin, CTO of MX Logic. 'Pharming is a malicious Web redirect,' in which a person trying to reach a legitimate commercial site is sent to the phony site without his knowledge. 'We don't have any hard evidence that pharming is happening yet,' Chasin said. 'What we do know is that all the ingredients to make it happen are in place.'
Oooh scary! The article is short on technical detail (but long on scary), but I think he's talking about DNS cache poisoning, whereby an attacker implants incorrect data in the victim's DNS cache, to cause them to visit the wrong IP address when they resolve a name. This Wired article (2005-03-14) seems to confirm this.
But wait! Another meaning is offered by Green Armor Solutions, who use the term to talk about the Panix and Hushmail domain hijacks, where an attacker social-engineered domain transfers from their registrars. There's no date on the page, but it appears to be post-March 2005.
Finally, yet another meaning is offered in this article at CSO Online: How Can We Stop Phishing and Pharming Scams? (May 2005): 'The Computing Technology Industry Association has reported that pharming occurrences are up for the third straight year.' What?! Call Scott Chasin!
Steady on -- it appears that the 'pharming' CSO Online is talking about, has devolved to the stage where it's simply a pop-up window that attempts to emulate a legit site's input -- no DNS trickery involved. (This trick has, indeed, been used in phish for years.)
So right there we have three different meanings for 'pharming', or four if you count the biotech one.
It may be impossible to get the marketeers to stop referring to 'pharming'. But please, if you're a techie, don't use that term, it's lack of clarity renders it useless. Anyway, the biotech people were there first, by several years...
Voting: None Dare Call It Stolen - Ohio, the Election, and America's Servile Press, by Mark Crispin Miller.
Miller and many others have obviously been spending a lot of work chasing down each incident in Ohio since last November, and there's quite a lot of them. It's impressive the degree to which recounts were evaded, if these allegations are true. There's many shocking cases alleged than I could really fit here -- but here's some of the lowest points:
On December 13, 2004, it was reported by Deputy Director of Hocking County Elections Sherole Eaton, that a Triad GSI employee had changed the computer that operated the tabulating machine, and had "advised election officials how to manipulate voting machinery to ensure that preliminary hand recount matched the machine count." This same Triad employee said he worked on machines in Lorain, Muskingum, Clark, Harrison, and Guernsey counties.
it strongly appears that Triad and its employees engaged in a course of behavior to provide "cheat sheets" to those counting the ballots. The cheat sheets told them how many votes they should find for each candidate, and how many over and under votes they should calculate to match the machine count. In that way, they could avoid doing a full county-wide hand recount mandated by state law.
In Union County, Triad replaced the hard drive on one tabulator. In Monroe County, "after the 3 percent hand count had twice failed to match the machine count, a Triad employee brought in a new machine and took away the old one. (That machine's count matched the hand count.)"
The willingness to throw away functioning, reliable election systems, and replacing them with new, easy-to-subvert ones, is astounding. But on top of that, when concerned parties investigate and find danger signs, it's easily buried:
Miller emphasizes that, even after the National Election Data Archive Project, on March 31, 2005, "released its study demonstrating that the exit polls had probably been right, it made news only in the Akron Beacon-Journal," while "the thesis that the exit polls were flawed had been reported by the Associated Press, the Washington Post, the Chicago Tribune, USA Today, the San Francisco Chronicle, the Columbus Dispatch, CNN.com, MSNBC, and ABC."
Miller's conclusion: 'the press has unilaterally disarmed'.
Friends: the ex-Iona readers, and those with an interest in urban design, might like to go take a look at citynoise.blogspot.com -- Lean Doody's new urban design weblog.
Open Source: so I was just looking at OSCON 2005's website, and I noticed that it listed Kim Polese, of SpikeSource, as a presenter.
I don't really pay any attention to what's happening in Java these days, but it appears that SpikeSource launched last year to provide 'enterprise support services for open-source software' with a Java/enterprise slant.
Funnily enough, my last encounter with a Kim-Polese-headed company did indeed have a big effect on me, open-source-wise.
That company was Marimba, and they made an excellent Java GUI builder called Bongo. In those days (nearly ten years ago!), I was working on a product for Iona as a developer, in Java and C++, and we needed to provide a GUI on a number of Java tools. I chose to use Bongo, as it had a great feature set and looked reliable.
Wow, was I wrong! The software was reliable -- sadly, the same couldn't be said about the vendor. What I hadn't considered was the possibility that the company might decide to discontinue the product, and not offer any migration help to its customers -- and that's exactly what happened, Sometime around 1998, Marimba decided that Bongo wasn't quite as important as their Castanet 'push' product, and dropped it. Despite calls from the Bongo-using community to release the code so that the community could maintain it and avoid code-rot, they never did, and as a result apps using Bongo had to be laboriously rewritten to remove the Bongo dependencies.
I learned an important lesson about writing software -- if at all possible, build your products on open source, instead of relying on a fickle commercial software vendor. It's a lot harder to have the rug pulled out from under you, that way.
Update: Well, it seems it was quite far off the mark about Marimba. Someone who worked at Marimba at the time read the blog entry, and got in touch via email:
I was an employee of Marimba in the early days, and was around when we developed Bongo, and still later, when we discontinued it, and still later, when Bongo *was* released to the open-source community (jm: appears to be around the start of 1999 I think). It was hosted on a site called freebongo.org and continued to be enhanced with new features and a lot of new and cool widgets. It was ultimately discontinued a few years later due to lack of interest.
It was hosted and primarily maintained in the open-source community by one of the original Bongo engineers. Here's a link from the Java Gazette from the days when it was called Free Bongo.
So don't go blaming Marimba. We did listen to our users and release the code!
Fair enough -- and they deserve a lot more credit than I'd initially assumed. I guess I must have missed this later development after leaving Iona. Apologies, ex-Marimbans!
Patents: This has come up twice recently in discussions of software patenting, so it's worth posting a blog entry as a note.
There's a common misconception that a patenter does not necessarily need to enforce a patent in the courts, for it to remain valid. This isn't true in the US at least, where there is the legal doctrine of 'laches', defined as follows in the Law.com dictionary:
Laches - the legal doctrine that a legal right or claim will not be enforced or allowed if a long delay in asserting the right or claim has prejudiced the adverse party (hurt the opponent) as a sort of 'legal ambush'.
The Bohan Mathers law firm have a good paragraph explaining this:
...the patent holder has an obligation to protect and defend the rights granted under patent law. Just as permitting the public to freely cross one's property may lead to the permanent establishment of a public right of way and the diminishment of one's property rights, so the knowing failure to enforce one's patent rights (one legal term for this is laches) against infringement by others may result in the forfeiture of some or all of the rights granted in a particular patent.
See also this and this page for discussion of cases where it was relevant. It seems by no means clear-cut, but the doctrine is there.
Spam: back from CEAS. The schedule with links to full papers is up, so anyone can go along and check 'em out, if you're curious.
Overall, it was pretty good -- not as good as last year's, but still pretty worthwhile. I didn't find any of the talks to be quite up to the standards of last year's TCP damping or Chung-Kwei papers; but the 'hallway track' was unbeatable ;)
Here's my notes:
AOL's introductory talk had some good figures; a Pew study reported that 41% of people check email first thing in morning, 40% have checked in the middle of the night, and 26% don't go more than 2-3 days without checking mail. It also noted that URLs spimmed (spammed via IM) are not the same as URLs spammed -- but the obfuscation techniques are the same; and they're using 2 learning databases, per-user and global, and the 'Report as Spam' button feeds both.
Experiences with Greylisting: John Levine's talk had some useful data -- there are still senders that treat a 4xx SMTP response (temp fail) as 5xx (permanent fail), particularly after end of the DATA phase of the transaction, such as an 'old version of Lotus Notes'; and there are some legit senders, such as Kodak's mail-out systems, which regenerate the body in full on each send, even after a temp fail, so the body will look different. He found that less than 4% of real mail from real MTAs is delayed, and overall, 17% of his mail traffic was temp-failed. The 4% of nonspam that was delayed was delayed with peaks at 400 and 900 seconds between first tempfail and eventual delivery.
As usual, there were a variety of 'antispam via social networks' talks -- there always are. Richard Clayton had a great point about all that: paraphrasing, I trust my friends and relatives on some things, and they are in my social networks -- but I don't trust their judgement of what is and is not spam. (If you've ever talked to your mother about how she always considers mails from Amazon to be spam, you'll know what he means.)
Combating Spam through
Legislation: A Comparative Analysis of US and European Approaches:
the EU 'opt-in' directive is now transposed everywhere in the EU;
EU citizens who are spammed by a citizen from another EU country,
the reports should be sent to the antispam authority in the sender's
country; and there's something called 'ECNSA', an EU contact network of
spam authorities, which sounds interesting (although ungoogleable).
Searching For John Doe: Finding Spammers and Phishers: MS' antispam attorney, Aaron Kornblum, had a good talk discussing their recent court cases. Notably, he found one cases where an Austrian domain owner had set up a redirector site which sounded like it was expressly set up for spam use -- news to me (and worrying).
A Game Theoretic Model of Spam E-Mailing: Ion Androutsopoulos gave a very interesting talk on a game theoretic approach to anti-spam -- it was a little too complex for the time allotted, but I'd say the paper is worth a read.
Understanding How Spammers Steal Your E-Mail Address: An Analysis of the First Six Months of Data from Project Honey Pot: Matthew Prince of Project Honeypot had some excellent data in this talk; recommended. He's found that there's an exponential relationship between google Page Rank and spam received at scraped addresses, which matches with my theory of how scrapers work; and that only 3.2% of address-harvesting IPs are in proxy/zombie lists compared to 14% of spam SMTP delivery IPs. (BTW, my theory is that address scraping generally uses Google search results as a seed, which explains the former.)
Computers beat Humans at Single Character Recognition in Reading based Human Interaction Proofs (HIPs): this presented some great demonstrations of how a neural network can be used to solve HIPs (aka CAPTCHAs) automatically. However, I'm unsure how useful this data is, given that the NN required 90000 training characters to achieve the accuracy levels noted in the paper; unless the attacker has access to their own copy of the HIP implementation they can run themselves, they'd have to spend months performing HIPs to train it, before an attack is viable.
Throttling Outgoing SPAM for Webmail Services: cites Goodman in ACM E-Commerce 2004 as saying that ESP webmail services are a 'substantial source of spam', which was news to me! (less than 1% of spam corpora, I'd guess). It then discusses requiring the submitter of email via an ESP webmail system to perform a hashcash-style proof-of-work before their message is delivered. By using a Bayesian spam filter to classify submitted messages, the ESP can cause spammers to perform more work than non-spammers, thereby reducing their throughput. Didn't strike me as particularly useful -- Yahoo!'s Miles Libbey got right to the heart of the matter, asking if they'd considered a situation where spammers have access to more than one computer; they had not. A better paper for this situation would be Alan Judge's USENIX LISA 2003 one which discusses more industry-standard rate-limiting techniques.
SMTP Path Analysis: IBM Research's anti-spam team discuss something very similar to several techniques used in SpamAssassin; our versions have been around for a while, such as the auto-whitelist (which tracks the submitter's IP address rounded to the nearest /16 boundary), since 2001 or 2002, and the Bayes tweaks we added from bug 2384, back in 2003.
Naive Bayes Spam Filtering Using Word-Position-Based Attributes: an interesting tweak to Bayesian classification using a 'distance from start' metric for the tokens in a message. Worth trying out for Bayesian-style filters, I think.
Good Word Attacks on Statistical Spam Filters: not so exciting. A bit of a rehash of several other papers -- jgc's talk at the MIT conference on attacking a Bayesian-style spam filter, the previous year's CEAS paper on using a selection of good words from the SpamBayes guys, and it entirely missed something we found in our own tech report -- that effective attacks will result in poisoned training data, with a significant bias towards false positives. In my opinion, the latter is a big issue that needs more investigation.
Stopping Outgoing Spam by Examining Incoming Server Logs: Richard Clayton's talk. Well worth a read. It's an interesting technique for ISPs -- detecting outgoing spam by monitoring hits to your MX from your own dialup pools which uses known ratware patterns.
Politics: EDRI-gram notes that the Firenze Linux User Group's server was tampered with last month at its ISP colo:
On Monday 27 June 2005, two members of FLUG (Firenze Linux User Group) visited the data centre of Dada S.p.a., in Milan, where the community server of the group is physically housed, in order to move it to another provider.
When the server was put out of the rack, however, it was discovered that the upper lid of the server case was half-opened. At a closer inspection, it was also discovered that the case lid was scratched, as if it had been put out and reinserted into the rack. Worse, the CD-ROM cable was missing, as were the screws that kept the hard disks in place.
What is particularly worrying is that the server hosted an anonymous remailer, whose keys and anonymity capabilities could have been compromised. Considering what happened to Autistici/Inventati server - which hosted another anonymous remailer - this possibility is not so far fetched. This begs the question whether a co-ordinated attempt at intercepting anonymous/private communications on the Internet has been ongoing in the past weeks and months.
Bizarre goings-on.
Hardware: After a few weeks running OpenWRT on a Linksys WRT54G, here's a status report.
Things that the new WRT54G running OpenWRT does a whole lot better than the Netgear MR814:
Man, that MR814 was a piece of crud. ;) I can't recommend OpenWRT enough...
Patents: A great outcome! The proposed Directive has been dropped, in the face of massive opposition. Coverage: /., FFII, FT.com, VNUnet, FSFE.
Unfortunately, Rocard's proposed amendments which would have turned this directive into a major win for us, didn't pass -- but it's still a good win. Software patents are not explicitly legal throughout Europe; although some jurisdictions do permit them, they're in a legal grey area, and prosecution is therefore hard (and very expensive for patent holders). This is a much better situation than if the directive as proposed by the Council had passed, since that would have explicitly legalised them throughout the EU.
On top of this win, what I find significant is that we've now brought the issue from where it was a few years ago, as a minor concern known only to a few uber-geeks, to a major political issue that made headlines around the globe. Even my local NPR affiliate reported on this decision! That's a far cry from the mid-90's, when I had a hard time explaining the point of theLeague for Programming Freedom to my hacker friends in the TCD Maths Department.
A great quote from the VNUnet article:
'This represents a clear victory for open source,' said Simon Phipps, chief open source officer at Sun Microsystems. 'It expresses Parliament's clear desire to provide a balanced competitive market for software.'
Yes, that's Sun saying that less software patenting is a good thing. Believe me, that's a great leap forward. Or check out Irish MEP Kathy Sinnott's amazing comments. She hits the nail right on the head; I'm very impressed by that speech.
Patents: I'm just back from a fantastic holiday weekend, totally offline, hiking through Catalina Island. I'm a little bit sunburnt, my nose is peeling, but it was great fun. I got a fantastic picture of the sun setting over hundreds of boats bobbing at their moorings in Two Harbors, which I must upload at some stage.
Anyway, it seems that over the weekend, the EU software-patents debate has swung back heavily towards the anti-swpat side. Fingers crossed -- the vote is this week.
Also, today, EUpolitix.com has an interview with Charlie McCreevy, quoting him as saying:
'The theme, or the background music, to both of these particular directives (the CII and Services Directives) you could see as part of, anti-globalisation, anti-Americanism, anti-big business protests -- in lots of senses, anti-the opening up of markets'
This is standard practice for the Irish government -- they did exactly the same thing with the e-voting issue, painting the ICTE as 'linked to the anti-globalisation movement'. (I have a feeling they think that any group organised online must be 'anti-globalisation', at this stage.)
Of course, with these accusations of being anti-free-market, it's important to remember that a patent is a government-issued monopoly on an invention (or in the software field, on an idea), in a particular local jurisdiction. If anything, being against software patenting is a pro-free-market position, one shared by prominent US libertarians; and nothing gets more pro-free-market than those guys. ;)
Spam: if you work in anti-spam, especially in filtering, or even just in working with email in general, it's well worth going to CEAS 2005, the Conference on Email and Anti-Spam, on Thursday July 21st and Friday 22nd in Stanford:
The organizers of the Conference on Email and Anti-Spam invite you to participate in its second annual meeting. This forum brings together academic and industrial researchers to present new work in all aspects of email, messaging and spam -- with papers this year covering fields as diverse as text classification, clustering and visualization of email, social network analysis applied to both email and spam, spam filtering methods including text classification and systems approaches, game theory, data analysis, Human Interactive Proofs, and legal studies, among others. The conference will feature 26 paper presentations, a banquet, and two invited speakers. See http://www.ceas.cc for details of the current program, as well as on-line registration.
Registration runs out on July 10th.
I went last year, and it was excellent -- several very interesting papers were presented. I'm going this year, too, along with quite a few SpamAssassin committers, and I'm looking forward to it.
Hardware: On my home network, I recently replaced my NetGear MR814 with a brand new Linksys WRT54G.
My top criteria for what hardware to buy for this job weren't price, form factor, how pretty the hardware is, or even what features it had -- instead, I bought it because it's an extremely hackable router/NAT/AP platform. Thanks to a few dedicated reverse engineers, the WRT hardware can now be easily reflashed with a wide variety of alternative firmware distributions, including OpenWRT, a fully open-source distro that offers no UI beyond a command-line.
Initially, I considered a few prettier UIs -- HyperWRT, for example -- since I didn't want to have to spend days hacking on my router, of all things, looking stuff up in manuals, HOWTOs and in Google. Finally I decided to give OpenWRT a spin first. I'm glad I did -- it turned out to be a great decision.
(There was one setup glitch btw -- by default, OpenWRT defaults to setting up WPA, but the documentation claims that the default is still no crypto, as it was previously.)
The flexibility is amazing; I can log in over SSH and run the iftop tool to see what's going on on the network, which internal IPs are using how much bandwidth, how much bandwidth I'm really seeing going out the pipe, and get all sorts of low-level facts out of the device that I'd never see otherwise. I could even run a range of small servers directly on the router, if I wanted.
Bonus: it's rock solid. My NetGear device had a tendency to hang frequently, requiring a power cycle to fix; this bug has been going on for nearly a year and a half without a fix from NetGear, who had long since moved on to the next rev of cheapo home equipment and weren't really bothering to support the MR814. I know this is cheap home equipment -- which is why I was still muddling along with it -- but that's just ridiculous. None of that crap with the (similarly low-cost) WRT. OpenWRT also doesn't contain code to DDOS NTP servers at the University of Wisconsin, which is a bonus, too. ;)
Sadly, I don't think Cisco/Linksys realise how this hackability is making their market for them. They've been plugging the security holes used to gain access to reflash the firmware in recent revisions of the product (amazingly, you have to launch a remote command execution attack through an insecure CGI script!), turning off the ability to boot via TFTP, and gradually removing the ways to reflash the hardware. If they succeed, it appears the hackability market will have to find another low-cost router manufacturer to give our money to. (update, June 2006: they since split the product line into a reflashable Linux-based "L" model and a less hackable "S" model, so it appears they get this 100%. great!)
Given that, it's interesting to read this interview with Jack Kelliher of pcHDTV, a company making HDTV video capture cards:
Our market isn't really the mass market. We were always targeting early adopters: videophiles, hobbyists, and students. Those groups already use Linux, and those are our customers.
Matthew Gast: The sort of people who buy Linksys APs to hack on the firmware?
Jack Kelliher: Exactly. The funny thing is that we completely underestimated the size of the market. When we were starting up the company, we went to the local Linux LUG and found out how many people were interested in video capture. Only about 2 percent were interested in video on Linux, so we thought we could sell 2,000 cards. (Laughs.) We've moved way beyond that!
Well worth a read. There's some good stuff about ulterior motives for video card manufacturers to build MPEG decoding into their hardware, too:
The broadcast flag rules are conceptually simple. After the digital signal is demodulated, the video stream must be encrypted before it goes across a user accessible bus. User accessible is defined in an interesting way. Essentially, it's any bus that a competent user with a soldering iron can get the data from. Video streams can only be decrypted right before the MPEG decode and playback to the monitor.
To support the broadcast flag, the video capture must have an encryptor, and the display card must have a decryptor. Because you can't send the video stream across a user accessible bus, the display card needs to be a full MPEG decoder as well, so that unencrypted video never has to leave the card.
Matthew Gast: So the MPEG acceleration in most new video cards really isn't really for my benefit? Is it to help the vendors comply with the broadcast flag?
Jack Kelliher: Not quite yet. Most video cards don't have a full decoder, so they can't really implement the broadcast flag. ATI and nVidia don't have full decoders yet. They depend on some software support from the operating system, so they can't really implement the broadcast flag. Via has a chipset with a full decoder, so it would be relatively easy for them to build the broadcast flag into that chipset.
Aha.
Work: I took a look over at Edd Dumbill's weblog recently, and came across this posting on planning programming projects. He links to another article and mentions:
My recent return to managing a team of people has highlighted for me the difficulties of the arbitrary deadline approach to project management. Unfortunately, it's also the default management approach applied by a lot of people, because the concept is easy to grasp.
The arbitrary deadline method is troublesome because of the difficulty of estimation. As John's post elaborates, you can never foresee all of the problems you'll meet along the way. The distressing inevitability of 90% of the effort being required by 2% of the deliverable is frequently inexplicable to developers themselves. Never mind the managers remote from the development!
I've been considering why my experience of working with open source seems generally preferable to commercial work, and this may be one of the key elements. Commercial software development is deadline-driven, whereas most open source development has not been, in my experience; 'it's ready when it's ready'.
Edd suggests that using a trouble-ticket-based system for progress tracking and management is superior. I'm inclined to agree.
Patents: yes, I keep rattling on about this -- the vote is coming up on July 6th. I promise I'll shut up after that ;)
UEAPME has issued a statement regarding the directive which is strongly critical of its current wording (UEAPME is the European small and medium-sized business trade association, comprising 11 million SMEs). Quote:
'The failure to clearly remove software from the scope of the directive is a setback for small businesses throughout Europe. UEAPME is now calling on the European Parliament to reverse yesterday's decision at plenary session next month and send a strong message that an EU software patent is not an option,' Hans-Werner Müller, UEAPME Secretary General, stated.
'There is growing agreement among all actors that software should not be patented, so providing an unequivocal definition in the directive that guarantees this is clearly in the general interest. We are calling on the Parliament to support the amendments that would ensure this,' said Mr Müller.
'The cacophony of misinformation and misleading spin from the large industry lobby in the run up to this vote has obscured the general consensus on preventing the patenting of pure software.'
That's all well and good. So presumably the Irish members of UEAPME, ISME and the SFA, are agreeing, right? Sadly, neither of these have issued any press releases on the subject, as far as I can see, and approaches by members of IFSO have been totally fruitless.
Since both have made recent press noting that Irish small businesses face difficulties with the rising costs of doing business, this would seem to be a no-brainer -- legalising software patents would immediately open Irish SMEs up to the costs associated with them: licensing fees, fighting spurious infringement litigation from 'patent troll' companies, the 'chilling effects' on investors noted by Laura Creighton, and of course the high price of retaining patent lawyers to file patents on your own innovations. One wonders why they aren't concerned about these costs...
Antarctic: Happy Midwinter's Day!
I've just finished reading Big Dead Place , Nicholas Johnson's book about life at McMurdo Base and the US South Pole Station, with anecdotes from his time there in the early years of this decade.
It's a fantastic book -- very illustrative of how life really goes on on a distant research base, once you get beyond romantic notions of exploration of the wild frontiers. (Like many geek kids, I spent my childhood dreaming of space exploration, and Antarctica is the nearest thing you can get to that right now.) A bonus: it's hilarious, too.
Unfortunately it's far from all good -- as one review notes, it's like 'M*A*S*H on ice, a bleak, black comedy.' There's story after story of moronic bureaucratic edicts emailed from comparatively-sub-tropical Denver, Colorado, ass-covering emails from management on a massive scale, and injuries and asbestos exposures covered up to avoid spoiling 'metrics'.
Here's a sample of such absurdity, from an interview with Norwegian world-record breaking Antarctic explorer, Eirik Sønneland:
BDP: I was working at McMurdo when you arrived in 2001. I remember it well because we were commanded by NSF not to accommodate you in any way, and were forbidden to invite you to our rooms or into any buildings. We were told not to send mail for you, nor to send email messages for you. While you were in the area, NSF was keeping a close eye on you. What did the managers say to you when you arrived?
They asked us what plans we had for getting home. The manager at Scott Base (jm: the New Zealand base) was calm and listened to what we had to say. I must be honest and say that this was not the way we were treated by the U.S. manager. It was like an interrogation. Very unpleasant. He acted arrogant. However, it seemed like he started to realize after a couple of days that we didn't try to fool anybody. He probably got his orders from people that were not in Antarctica at the time. And, to be honest, today I don't have bad feelings toward anyone in McMurdo. Bottom line, what did hurt us was that people could not think without using bureaucracy. If people could only try to listen to what we said and stop looking up paragraphs in some kind of standard operating procedures for a short while, a lot could have been solved in a shorter time.
One example: our home office, together with Steven McLachlan and Klaus Pettersen in New Zealand, got a green light from the captain of the cargo ship that would deliver cargo (beer, etc.) to McMurdo, who said he would let us travel for free back to New Zealand if it was okay with his company. At first the company was agreeable, but then NSF told them that the ship would be under their rent until it left McMurdo and was 27 km away. Reason for the 27 km? The cargo ship needed support from the Coast Guard icebreaker to get through the ice. Since, technically, the contract with NSF did not cease until the ship left the ice, NSF could stop us from going on the ship. At which point NSF offered to fly us from McMurdo for US$50,000 each.
He also maintains an excellent website at BigDeadPlace.com, so go there for an idea of the writing. BTW, it appears the UK also maintains an Antarctic base. Here's hoping they keep the bureaucracy at a saner level over there.
Patents: One of the key arguments in favour of the new EU software patenting directive as it's currently worded, from the 'pro' side, is that it doesn't 'allow software patents as such', since it requires a 'technical' inventive step for a patent to be considered valid.
Various MEPs have tried to clarify the meaning of this vague phrase, but without luck so far.
Coverage has mostly noted this as meaning that 'pure software' patents are not permissible, for example this Washington Post article, FT.com,and InformationWeek.
But is this really the case, in pragmatic terms? What does a 'technical inventive step' mean to the European Patent Office?
Well, it doesn't look at all promising, according to this report from the Boards of Appeal of the European Patent Office from 21 April 2004, dealing with a Hitachi business method patent on an 'automatic auction method'. The claims of that patent application (97 306 722.6) covered the algorithm of performing an auction over a computer network using client-server technology. The actual nature of this patent isn't important, anyway -- but what is important is how the Boards of Appeal judge its 'technical' characteristics.
The key section is 3.7, where the Board writes:
For these reasons the Board holds that, contrary to the examining division's assessment, the apparatus of claim 3 is an invention within the meaning of Article 52(1) EPC since it comprises clearly technical features such as a "server computer", "client computers" and a "network".
So in other words, if the idea of a computer network is involved in the claims of a patent, it 'includes technical aspects'. It then goes on to discuss other technical characteristics that may appear in patents:
The Board is aware that its comparatively broad interpretation of the term "invention" in Article 52(1) EPC will include activities which are so familiar that their technical character tends to be overlooked, such as the act of writing using pen and paper.
So even writing with a pen and paper has technical character!
It's a cop-out, designed to fool MEPs and citizens into thinking that a reasonable limitation is being placed on what can be patented, when in reality there's effectively no limits, if there's any kind of equipment involved beyond counting on your fingers.
The only way to be sure is to ensure the directive as it eventually passes is crystal clear on this point, with the help of the amendments that the pro-patent side are so keen to throw out.
(BTW, I found this link via RMS' great article in the Guardian where he discusses software patenting using literature as an analogy. recommended reading!)
Perl: double-encoding is a frequent problem when dealing with UTF-8 text, where a UTF-8 string is treated as (typically) ISO Latin-1, and is re-encoded.
utf8lint is a quick hack script which uses perl's Encode module to detect this. Feed it your data on STDIN, and it'll flag lines that contain text which may be doubly-encoded UTF-8, in a lintish way.
Science: in April and May, the New Yorker printed an amazing series of articles on climate change by Elizabeth Kolbert, full of outstanding research and interviews with the key players.
Unlike much coverage, it includes the expected results of climate change in the US:
Different climate models offer very different predictions about future water availability; in the paper, Rind applied the criteria used in the Palmer index to GISS's model and also to a model operated by NOAA's Geophysical Fluid Dynamics Laboratory. He found that as carbon-dioxide levels rose the world began to experience more and more serious water shortages, starting near the equator and then spreading toward the poles. When he applied the index to the giss model for doubled CO2, it showed most of the continental United States to be suffering under severe drought conditions. When he applied the index to the G.F.D.L. model, the results were even more dire. Rind created two maps to illustrate these findings. Yellow represented a forty-to-sixty-per-cent chance of summertime drought, ochre a sixty-to-eighty-per-cent chance, and brown an eighty-to-a-hundred-per-cent chance. In the first map, showing the GISS results, the Northeast was yellow, the Midwest was ochre, and the Rocky Mountain states and California were brown. In the second, showing the G.F.D.L. results, brown covered practically the entire country.
'I gave a talk based on these drought indices out in California to water-resource managers,' Rind told me. 'And they said, 'Well, if that happens, forget it.' There's just no way they could deal with that.'
He went on, 'Obviously, if you get drought indices like these, there's no adaptation that's possible. But let's say it's not that severe. What adaptation are we talking about? Adaptation in 2020? Adaptation in 2040? Adaptation in 2060? Because the way the models project this, as global warming gets going, once you've adapted to one decade you're going to have to change everything the next decade.
And how the anti-climate-change side are attempting to control US public opinion:
The pollster Frank Luntz prepared a strategy memo for Republican members of Congress, coaching them on how to deal with a variety of environmental issues. (Luntz, who first made a name for himself by helping to craft Newt Gingrich's 'Contract with America,' has been described as 'a political consultant viewed by Republicans as King Arthur viewed Merlin.') Under the heading 'Winning the Global Warming Debate,' Luntz wrote, 'The scientific debate is closing (against us) but not yet closed. There is still a window of opportunity to challenge the science.' He warned, 'Voters believe that there is no consensus about global warming in the scientific community. Should the public come to believe that the scientific issues are settled, their views about global warming will change accordingly.'
They're a great synthesis. Go read the articles -- part 1 ('Disappearing islands, thawing permafrost, melting polar ice. How the earth is changing'), part 2 ('The curse of Akkad'), and part 3 ('What can be done?'). They're long, but if you're still on the fence about this one, they'll wake you up.
Spam: via John Graham-Cumming's excellent anti-spam newsletter this month, comes a very cool animation of the dbacl Bayesian anti-spam filter being trained to classify a mail corpus. Here's the animation:

And Laird's explanation:
dbacl computes two scores for each document, a ham score and a spam score. Technically, each score is a kind of distance, and the best category for a document is the lowest scoring one. One way to define the spamminess is to take the numerical difference of these scores.
Each point in the picture is one document, with the ham score on the x-axis and the spam score on the y-axis. If a point falls on the diagonal y=x, then its scores are identical and both categories are equally likely. If the point is below the diagonal, then the classifier must mark it as spam, and above the diagonal it marks it as ham.
The points are colour coded. When a document is learned we draw a square (blue for ham, red for spam). The picture shows the current scores of both the training documents, and the as yet unknown documents in the SA corpus. The unknown documents are either cyan (we know it's ham but the classifier doesn't), magenta (spam), or black. Black means that at the current state of learning, the document would be misclassified, because it falls on the wrong side of the diagonal. We don't distinguish the types of errors. Only we know the point is black, the classifier doesn't.
At time zero, when nothing has been learned, all the points are on the diagonal, because the two categories are symmetric.
Over time, the points move because the classifier's probabilities change a little every time training occurs, and the clouds of points give an overall picture of what dbacl thinks of the unknown points. Of course, the more documents are learned, the fewer unknown points are left.
This is an excellent visualisation of the process, and demonstrates nicely what happens when you train a Bayesian spam-filter. You can clearly see the 'unsure' classifications becoming more reliable as the training corpus size increases. Very nice work!
It's interesting to note the effects of an unbalanced corpus early on; a lot of spam training and little ham training results in a noticeable bias towards the classifier returning a spam classification.
Web: a while back, I posted some musings about a web service to help authenticate users as members of a private group, similarly to how TypeKey authenticates users in general.
Well, Flickr have just posted this draft authentication API which does this very nicely -- it now allows third-party web apps to authenticate against Flickr, TypeKey-style, and perform a limited subset of actions on the user's behalf.
This means that using Flickr as a group authentication web service is now doable, as far as I can see...
Hardware: I've been needing a decent backup solution, since I've got 60GB of crud on my hard disk that isn't being rsynced offsite yet. So I bought myself a nifty DVD writer from woot.com a week ago, supporting DVD+RW, DVD+R, DVD-RW, and DVD-R, and a spindle of 20 DVD+Rs from Target. Little did I realise the world of pain I was entering.
Did you know there are no less than 6 barely-compatible DVD formats? Prerecorded DVD, DVD-RAM, DVD-R, and DVD-RW, from the DVD Forum, and DVD+RW and DVD+R, from the 'DVD+RW Alliance'. Interoperability is, needless to say, a total mess, even with the Sony 4-format drive I picked up.
I eventually managed to burn myself a DVD+R backup of bits of my home dir, making several coasters in the process (DVD+Rs apparently do not support simulated-write dry-runs, at least not with growfs). So, great!
Next thing to do was try it out on my laptop's internal CD/DVD drive to make sure it worked. Needless to say, it didn't.
Apparently, single-session, single-track DVD+Rs are virtually identical to DVD-ROMs, which most generic DVD-reader drives support. However, Sony drives do not support setting the 'book type' bits, which is the trick that turns a DVD+R 'into' a DVD-ROM-compatible disc. Guess why (hint: it's Sony). Yep, that's right, paranoia about piracy. Well, thanks a bunch, Sony -- my backups are now of decidedly limited usefulness, since I don't know if I'm ever going to be able to read them again! (more info from the OSTA.) I think I now see why Woot were flogging them cheap.
I'm not sure where to go with this -- do I have a spindle of 17 shiny frisbees? I have a very nasty feeling I'm heading into dead media territory here. What a mess...
Aaaanyway. Here's some possibly-useful bookmarks.
OTOH, I got to watch the BBC's new documentary, The Power of Nightmares, a fantastic history of the two parallel ideological worlds of al-Qaeda and the US neo-conservatives. Mind-boggling, but highly recommended.
Linux: the MythTV hacking continues (infrequently). Here's the latest -- a way to play music from my laptop, with sound output via the Mythbox.
Web: i caught sight of (8 June 2005, Interconnected), on the geographical insularity of the dot-com boom. A good read:
The huge influx of cash at the turn of the millennium led to the whole Web being built in the image of the Bay area. The website patterns that started there and - just by coincidence - happened to scale to other environments, those were the ones that survived.
Lots to think about. He's spot on, of course -- many of the web's big commercial success stories are almost shamelessly US-oriented, and if they work outside that, it's purely by accident.
I'd love to see more web businesses that work well for other parts of the world, but that'll take money -- and from what I saw in Dublin, the money either (a) just isn't there, or (b) frequently goes to the companies that talk the talk, but then piddle it away on ludicrous 'e-business architectures' and get nothing useful out the other end.
On both counts, Silicon Valley has an ace up its sleeve. The VCs are smart and well-funded, and the developers have experience, and know which tools are right for the job.
I'd be curious to hear how other high-tech hotspots in the US (Boston, for example) find this.
Web: I link-blogged this, but it's generated some email already, so it deserves a proper posting.
One thing you quickly learn about IBM where software patents are concerned, is that if IBM Research is making noise about a new software technique, they've probably patented it already. A few years ago, IBM was keen on HTTP transcoding -- rewriting web content in a proxy, to be more suitable for display and access from less-capable devices, like PDAs and mobile phones.
So I probably should not have been surprised today when I came across USPTO patent 6,886,013, which is an IBM patent on a 'HTTP caching proxy to filter and control display of data in a web browser'. It was applied for on Sep 11 1997, and finally granted on Apr 26 of this year.
The first claim covers:
A method of controlling presentation on a client of a Web document formatted according to a markup language and supported on a server, the client including a browser and connectable to the server via a computer network, the method comprising the steps of:
as the Web document is received on the client, parsing the Web document to identify formatting information;
altering the formatting information to modify at least one display characteristic of the Web document; and
passing the Web document to the browser for display.
Notice that there's actually no mention of a HTTP proxy there -- in other words, an in-browser rewriting element, such as Greasemonkey or Trixie may be covered by that claim. However, the claim does indicate that the document is passed from the 'client' to the 'browser', so perhaps having the 'client' inside the 'browser' evades that.
It appears this really wasn't original research even when the patent was applied for -- there's probable prior art, even if the patent itself doesn't cite it. For example, WWW4 in 1995 included Application-Specific Proxy Servers as HTTP Stream Transducers, which discusses 'transduction' of the HTTP traffic and gives an example of 'A ``rewriting'' OreO (transducer element) that encapsulates each anchor inside the Netscape Blink extension, making anchors easier to spot on monochrome displays'. On top of that, Craig Hughes notes that his 'senior project at Stanford in 1992 was an implementation of a content-modifying HTTP proxy. It re-worked HTML in http streams to add some markup to enable full navigability through touch screen or voice control, for screen-only kiosks.'
Add this to the ever-growing list of over-broad software patents.
Linux: Linux sound is
still a mess. Due to the ever-changing 'sound server of the week'
system used to decide how an app should output sound, it's perfectly
possible to have 3 apps on your desktop happily making noise at the same
time, while another app complains about requiring exclusive access to
/dev/dsp -- or worse, hangs silently while it attempts to grab
an exclusive lock on the device.
This page gives a
reasonably good guide to getting software mixing working across
(virtually) all apps, using ALSA software mixing and esd.
However, some cases are still very kludgy -- in particular, JuK, the excellent KDE mp3 jukebox app, has a tendency to play poorly with others, requiring playback via no less than two sound servers -- artsd and esd -- to work correctly in the above setup. In addition, the support for mp3 files in artsd is buggy -- it's frequently unable to open certain mp3s, depending on how they were encoded.
Well, good news -- the current release of JuK now supports direct playback from GStreamer via ALSA. Here's how. By adding these lines:
[GStreamerPlayer] SinkName=alsasink
to ~/.kde/share/config/jukrc, you can skip sending JuK mp3
playback via 2 sound servers, and just play directly to the hardware
from the mp3 player. An improvement! Not quite optimal, and
certainly not user-friendly -- but getting there...
Patents: in a recent discussion about games and patents, it emerged that these common elements are patented:
Looks like software patenting is coming to computer games in a big way. I'm not sure how any game on a modern platform can avoid the 'streamed loading' patent.
Naturally, I can remember playing games on the Commodore 64 in the 1980s that included these...
Life: seeing as yesterday was World No Tobacco Day, it's worth noting that I gave up smoking last Thursday.
 This is the first time I've taken the
step of quitting with any seriousness. I've been smoking since I was 18
or 19, without any real attempts to quit before now. It was a gradual
process, but imagining a smoker's future, with the diseases and reduced
life expectancy it involves, makes it quite sensible in the end. So far,
it's going pretty well -- lots of occasional pangs, but nothing I can't
say no to... especially with the aid of Liquorice Altoids. wish me luck!
This is the first time I've taken the
step of quitting with any seriousness. I've been smoking since I was 18
or 19, without any real attempts to quit before now. It was a gradual
process, but imagining a smoker's future, with the diseases and reduced
life expectancy it involves, makes it quite sensible in the end. So far,
it's going pretty well -- lots of occasional pangs, but nothing I can't
say no to... especially with the aid of Liquorice Altoids. wish me luck!
Net: Fergus Cassidy reports that 'bandwidth-starved TDs and Senators' in the Oireachtas will be taking a shortcut around Ireland's woeful consumer broadband situation, especially in terms of deployment outside of the main urban areas.
There's a tender up to implement 'an enhanced remote access system, which will improve access from Members' homes or constituency Offices to data and services on servers in Leinster House'.
No similar luck for their constituents, of course. That really takes the biscuit...
Security: the use of backscatter x-ray scanners has hit the US press now that the TSA are taking an interest.
These are interesting devices; unlike normal X-rays, they effectively render clothes invisible. That's obviously got big privacy implications.
Quite a few of the press stories include images that have been blurred or obscured, presumably to render them printable. However, this image seems closer to the real results (not work-safe).
They were trialled in Heathrow's Terminal 4 last year. One slashdotter's experience:
Every Nth person in the line had to go through. They take you to a seperate are which is blocked off, make you lift up your arms and then move, facing three different directions. There was one operator and the screen was blocked off. The operator is always the gender of the person being scanned. Still I felt very offended for two reasons. First, even though it was enclosed it still made me feel exposed and my personal space violated, second, any questions I asked the operator with regards to their data storage, or if I could see the images that had been made were met with ignorance and my questions were ignored. However, turning down a scan you would probably get a strip search which would be even worse. I disliked airplane security checks before, but now it is incredibly annoying.
The Times has some passenger's reactions to images from their scans:
'I was quite shocked by what I saw,' said Gary Cook, 40, a graphic designer from Shaftesbury, Dorset. 'I felt a bit embarrassed looking at the image.'
A female passenger, who did not want to be named, said: 'It was really horrible. It doesn't leave much to the imagination because you're virtually naked, but I guess it's less intrusive than being hand searched.'
If these are installed more widely, I wonder how long it'll take before we start seeing backscatter images of supermodels being saved to floppy by unscrupulous staff, and leaked?
Also, SpyBlog notes that images of children scanned with this device would constitute 'making, distributing or possessing child pornography' in the UK, presuming the machine stores them internally in electronic form. oops!
Apache: It seems I've been elected as a member of the Apache Software Foundation! That's a nice surprise ;)
Security: Adam Shostack has been tracking the immense volume of recent bank disclosures of compromised customer data. Bruce Schneier has also commented, and an interesting question arose in his posting's comments -- why are there seemingly no similar problems with European banks?
One responder points to a WSJ article which broadly misses the point. It discusses the additional layers of security imposed by European banks above the usual username/password combo. This is true -- Eurobanks generally have higher security at the 'front gate'; for example, I recall Bank of Ireland even issued SecurID-type tokens in its earliest online banking system. However, that misses the 'insider' attack, as in the most recent case of these 676,000 accounts, so I think it misses the point.
Bruce Schneier's take:
Personal data is 1) not collected as widely, and 2) much less valuable as a tool to commit fraud. The second reason is far more important.
I think he's partially right. Access to new and existing accounts in the US often requires little more than an SSN or similar trivial, easily-discoverable, data which is used in common across multiple institutions, and can be performed online; whereas in Europe, one requires documentary proof of address, ID, and the act must be performed in person at a bank branch. (This is often exceedingly annoying, of course. ;) In general, identity theft seems to be at a greater level in the US, and this is one reason why, I'd guess.
Adam Shostack has another take: these disclosures have all arrived on the heels of California's SB 1386. It's very unlikely that these kind of breaches never occurred before this, and suddenly began recently -- it's more likely that they've always gone on, but are unreported in Europe (and of course were unreported in the US, pre-SB 1386).
I'd add another point -- the US has a large population of targets, with banks sharing financial systems across the entire country. Europe, by contrast, has many individual countries which each have their own set of banks and banking systems, and less interoperability and cross-state data flow. The potential return from ID theft fraud is increased by the larger pool of candidate victims in the US, compared to what an attacker could achieve in each individual European country. This means both that (a) an attack will affect a smaller number of victims in Europe than the US, and (b) widening the scale of an attack becomes significantly harder when the attacker must deal with new systems. It's the 'security monoculture' issue again, applied to banking instead of operating systems.
Hardware: Slashdot: Nokia's Linux Handheld. It's to be called the Nokia 770 Internet Tablet, and runs on an open source development platform called Maemo.
This looks really nifty. ARM processor, 800x480 pixel resolution, GTK+, 2.6 kernel, wifi, 3 hours of active battery life, and a clever panning system to get around the clunkiness of scrollbars on a touchscreen.
I note particularly that they seem to have planned to include an RSS reader based on Liferea.
The Maemo site looks interesting, in
that it's clearly a bunch of switched-on, open-source-comprehending
developers who set it up; it's built using Apache Forrest, they use
Bugzilla for issue tracking, Mailman for lists, the terms of use
for user contributions explicitly call out OSI-approved licenses as a
requirement, there's plentiful references to Debian's apt as the
preferred means of installing developer platform software, and Maemo
apps are distributed as Debian packages.
There's clearly been quite a lot of work going on behind the scenes. There's already some third-party apps out there, such as those on INdT's Maemo apps page, and the the SDK tutorial contains copious detail, suggesting it's been seeing some use.
That SDK tutorial is full of tantalizing glimpses into Maemo's operation.
It all looks very promising, and nicely hackable! I'm looking forward to a closer look at one of these. It's especially good to see such a solid comprehension of the open source model by such a major company. (If only they could have a word with their patents department ;)
Update: They've ported WebCore to GTK+. Mobile Gazette has more info, too, including this worrying line:
And although Nokia hold several patents for (the Maemo development platform), they intent to open up access to their intellectual property to aid development.
(My emphasis.) That line is not encouraging, seeing as it seems to be a pretty typical cross-compilation platform as seen in embedded systems development. But hey, let's see the patents first.
Clothing: I love Threadless. Unfortunately, they don't have an RSS feed for new T-shirts. So I wrote a quick scraper:
with pictures, naturally. This is not going to help my Threadless habit. ;)
Here's a preview of what the feed looks like:
Weblogs: there's been a few attempts to mine 'trend' data from del.icio.us:
However, none consider how many links a user generates. A user who links to every single page on the web would quickly gain a good 'trendsetting' rating, and would also skew the website trends upwards, without actually providing useful data to others.
A look at the hublog top posters does seem to indicate they're linking prolifically to any old crap that looks likely to be popular, which is a more humanly-possible way to do that. ;)
However, populicious new links is quite cool -- popular sites that are new in the last 24 hours. Especially handy to find out where one could download Daily Show torrents these days. ;)
There's also the venerable Hot Links, which unfortunately tracks a very small population, but still gets interesting stuff.
Mr. Justice Bradley, discussing US patent law in 1882:
The design of the patent laws is to reward those who make some substantial discovery or invention, which adds to our knowledge and makes a step in advance in the useful arts. Such inventors are worthy of all favor. It was never the object of those laws to grant a monopoly for every trifling device, every shadow of a shade of an idea, which would naturally and spontaneously occur to any skilled mechanic or operator in the ordinary progress of manufactures.
Such an indiscriminate creation of exclusive privileges tends rather to obstruct than to stimulate invention. It creates a class of speculative schemers who make it their business to watch the advancing wave of improvement, and gather its foam in the form of patented monopolies, which enable them to lay a heavy tax upon the industry of the country, without contributing anything to the real advancement of the arts. It embarrasses the honest pursuit of business with fears and apprehensions of concealed liens and unknown liabilities to lawsuits and vexatious accountings for profits made in good faith.
Well said that man! (via)
Computing: mentioned in a Slashdot thread about green server farms -- a page extolling the OpenVPS virtual-server software's environmental benefits:
OpenVPS is good for the environment: a low-end server these days consumes no less than 200W. Given that typical servers run 24/7/365 this amounts (to) 1752 KWh per year. And because every joule of energy consumed by a server is transformed to heat, you need to at least double this to consider the air conditioning costs, which brings us to 3504 KWh per year. ...
At some point this becomes an ethical question: If my CPU is 99.9% idle, is it environmentally (not to mention fiscally!) responsible of me to keep this server running?
Virtualization technologies such Linux VServer used by OpenVPS offer a very viable alternative. If the server acts and feels like a dedicated server, what difference does it really make if it's actually virtual? Yet consolidating 30 physical servers into 30 OpenVPS accounts running on one (albeit power hungry) server would save over 100000 kWh per year. That's as much energy as is consumed on average by 10 houses!
What an excellent point! The OpenVPS dev's slashdot commment reveals another good demo of this --
# cat /proc/uptime 16000520.62 9482790.31
The first number is seconds of uptime, the second number is seconds spent in a CPU-idle state. So the server for taint.org, going by those numbers, has spent 59% of its time in a CPU-idle state -- and converting fossil fuels to waste heat in the process...
Spam: About this time last year, German neo-nazis launched a massive worldwide spam run with the aid of the Sober.H worm.
Well, it looks like they're planning to make this a regular occurrence, because it's on again, spamming nazi opinions linking to stories on reputable news sites, as well as pages on less reputable right-wing sites, Joe Wein has posted some samples. I've already received nearly a thousand since last night.
The good news -- here's a SpamAssassin ruleset that catches these nicely. thanks Raymond!
Dublin: Sorry to the non-Dublin readership, I'm sure you all are getting quite bored of this by now. But anyway...
According to jd on the discussion page, the new owner of the Stag's Head is Louis Fitzgerald, who picked it up for EUR 5.8 million.
Reportedly, he's 'the biggest publican in Dublin' (sic), and owns The Quays in Temple Bar, The Palmerstown House in Palmerstown, The Big Tree on Dorset Street and The Poitin Stil in Rathcoole -- and Kehoe's on South Anne Street. Quite an empire.
I'll have to leave the speculation on Fitzgerald's pros and cons to more recent residents of Dublin, but I agree with jd's comment: 'hope he does half a good as job as the Shaffrys, and the bicycles are left outside rather than on the ceiling,' Amen to that.
TV: I've taken a little time to throw up my PVR build log.

If you're hacking on one yourself, or curious about what it takes, or just like reading cut-and-pasted UNIX command lines -- go take a look!
UNIX: a quick recap of a good tip combo picked up from ILUG recently. To paraphrase Conor Wynne's original question:
What's the best way to set up a secure connection between two hosts, possibly over the internet, using SSH, suitable for use from cron so that it can run via crontab without entering authentication manually?
Barry O'Donovan replied:
I suggested ssh keys without passphrases ... in
http://www.barryodonovan.com/publications/lg/104/ and it includes instructions. ... You can invoke rsync over ssh and specify a specific key with:rsync -a -e 'ssh -i /home/username/.ssh/id_rsa-serverbackup'
Colm MacCárthaigh followed up with:
You can restrict what commands an ssh account can run in the ssh public key. This is how some of our more important projects (like Debian, FreshRPMS, and a few more) push us updates. The key looks like (jm: all on one line, no space between 'no-pty,' and 'command'):
no-port-forwarding,no-X11-forwarding,no-agent-forwarding,no-pty, command="/home/ximian/rsync-ximian-nolog &"
ssh-dss keydata username@blahSo, create a passwordless public key like so, and just change the command to whatver rsync runs.
Combined, that's a useful tip -- I knew about the ssh command restriction technique, but being able to use a specific single-purpose key from the ssh client is very useful.
(updated: mbp mailed to note some missing quotes in Barry's command above; they'd been eaten by WebMake. drat.)
UNIX: another useful tip. Bash supports a wide variety of command line editing tricks; you have the usual GUIish editing (backspace, insert new characters, delete, blah blah) through the GNU Readline library, and in addition to that you have the traditional csh-style history expansion (like '!!' to refer to the previous command typed).
The latter are great, but they won't actually be expanded until you hit Enter and run the command line. That can be inconvenient, resulting in the user being forced to reach for the rodent for some cut'n'paste instead.
Here's a handy trick -- add this line to ~/.inputrc (creating the
file if necessary):
Control-x: shell-expand-line
Start a new bash shell. Now, if you type CTRL-X during command line entry, any shell metacharacters will be expanded on the current command line. For example:
% echo Hello world
Hello world
% echo Hi !$ (press CTRL-X)
(current command line expands to:)
% echo Hi world
There's a
few more commands supported, but none of them are really quite
as useful as shell-expand-line.
Update: 'Smylers' wrote to point me at this UKUUG talk from 2003 which discusses .inputrc expansions, and provides some insanely useful tips.
In particular, Magic Space clearly knocks this tip into a cocked hat, by performing the expansion on the fly as you type the command, with no additional keypresses -- amazing! Bonus: it works if you use Emacs-mode line editing as well as Vi-mode.
I strongly recommend reading that paper -- lots of other good tips there.
Patents: New Scientist: Sony patent takes first step towards real-life Matrix:
IMAGINE movies and computer games in which you get to smell, taste and perhaps even feel things. That's the tantalising prospect raised by a patent on a device for transmitting sensory data directly into the human brain - granted to none other than the entertainment giant Sony.
It's a very lame 'first step' though -- Sony has done no research and development on this invention whatsoever, it's just a patent form of the old 'in the future, we'll wear tinfoil suits! And here's how they'll probably work!' speculation. Sony's comment:
Elizabeth Boukis, spokeswoman for Sony Electronics, says the work is speculative. 'There were not any experiments done,' she says. 'This particular patent was a prophetic invention. It was based on an inspiration that this may someday be the direction that technology will take us.'
That's nice; I'm sure they have some in the pipeline for flying cars, too.
It's good to know that if an inventor does eventually come up with an ultrasound-based human-computer brain interface, they'll have to pay license fees to Sony so they can use their 'prophecy' in their invention. The USPTO's high standards are being maintained, as usual...
Ireland: Worth watching for european software-patent watchers, Forfás, Ireland's 'national policy advisory board on enterprise, trade, science, technology and innovation' are running a series of monthly seminars on 'Intellectual Property' in association with Licensing Executives Society Britain and Ireland.
This one looks quite interesting -- 10 June: 'Patenting Software - The Current State of Play', Author Barry Moore, of Hanna Moore & Curley, patent attorneys.
Interested parties can attend with pre-registration, or wait to download the mp3 at Forfás' website, apparently, along with the rest of the lecture series. (No sign what the license is on those files, though ;)
Patents: It seems the Irish Software Association has a new chairperson, namely Bernadette Cullinane. Whether this has anything to do with Cathal Friel's 'out of line' statements, who knows...
John McCormac passed on some interesting quotes from an Irish Times interview, which were also syndicated here:
'The incoming chairwoman of the Irish Software Association (ISA), Bernie Cullinane, has pledged to support the introduction of a proposed European Union directive on software patents.
She also warned members of the European parliament against blocking the controversial new directive or weakening it by proposing a host of amendments. ...
Ms. Cullinane, a former chief operating officer of the Irish company Performix said European firms needed to protect their intellectual property in a similar manner to the way US firms can.
'We don't want any further dilution of the current situation on patents,' she said in an interview with The Irish Times following her ratification as chairwoman of the ISA last night.'
My emphasis -- given that the current situation is that they are unenforceable in Europe, that's good, because we on the other side don't want a dilution either!
'We do need to look at how the US is developing its software industry and a removal of the patent (sic) could weaken venture capitalists' appetites for investing in new innovative companies.'
The whole 'venture capital requires patents' line is easily debunked. I'm sure the VC companies are telling Ms. Cullinane that they want patents, of course; it's just that they're wrong. ;) Laura Creighton, a European investor, gave a fantastic speech in Brussels in 2003 about investment and patents:
Software Patents (in the US in the 1990s) encouraged venture capitalists to make foolish investments, because they believed the patents were worth something. Venture capitalists often do not mind if the companies where they have invested go bankrupt -- as long as they hold title to the patents. They can start over again with a different team.
Sadly, when the bubble burst, the venture capitalists discovered that their patents were only good for a trip to court -- or at least some legal wrangling with a bunch of lawyers. A software patent is not like a hardware patent, where typically one, or at most a few covers the whole invention. Dozens, sometimes hundreds of patents, are relevant to any piece of software. So an investor, who now owns the assets of a defunct company -- cannot take its patents and hand them to a new development team and say 'build this'. It is impossible to develop software today without infringing somebody's American patent.
The venture capitalists, having lost fortunes backing companies which had no real product, are now uninterested in investing in any software companies whatsoever. Right now the American economy could benefit from more investment -- but the capital is not going into software companies. Again, part of the problem is software patents. The venture capitalists have learned that all software is in violation of somebody's patent. So they do not want to touch the stuff. Thus on the up side, and the down side, the existence of software patents have contributed to creating the stock bubble, and making the recovery slower and harder than it needed to be. So #4 is right out -- the existence of software patents are inhibiting investment right now, and for very good reason.
In other words, the presence of software patents has 'weakened venture capitalists' appetites for investing in new innovative companies', as Ms. Cullinane put it.
Anyway -- to keep the VCs happy, small companies can still obtain software patents in the US, and spend the tens of thousands of dollars required to register and enforce them in court, if they so desire. They can bring the US software industry to a legal standstill if they like, as they seem to have done, as long as European software developers can quietly carry on developing software for use outside the US ;)
But at least things aren't as bad as the situation with my neighbours -- I live a few miles from the offices of Acacia Research, the notorious patent trolls, who've just initiated a new lawsuit against Intel and TI.
Reportedly however, they're planning to open a European office this quarter...
Privacy: after reading Adam Shostack's weblog posting about private/anonymous blogging, I've been driven to think about that, and would up writing up a case study of Cogair, which was an influential anonymously-published proto-weblog in Ireland in the '90s.
Now, quinn at ambiguous.org quotes a review of EFF's recent 'anonymous blogging' guidelines, which largely comes up with one conclusion: it's a usability nightmare. The problem is, the EFF report recommends using invisiblog.com, which in turns uses the Mixmaster remailers. Those things are awful, and I doubt anyone but their authors could possibly know how to use them ;)
Here's an easier way to blog anonymously. I haven't tried it (honest ;) but from keeping up on this stuff, it should work...
Firefox
Tor
Hushmail
Blogger
This is essentially the 'TOR to blog server' method described at the privateblogging wiki.
Now, note that along that chain we have 3 levels of identity -- the IP address (hidden by Tor), the email address (traceable to Hushmail, who could conceivably give up the Tor router's IP), and the Blogger.com weblog site (traceable to Blogger, who could give up the Hushmail address and the Tor router's IP).
As long as you don't give it away in your writings on that weblog -- and as long as Tor remains safe -- your own identity in turn is safe, too; and Tor has proved safe, so far.
There are still problems:
PS, for the future: the guys behind Tor are working on a replacement for Mixmaster anonymous remailer software, called Mixminion. There's also a wiki for discussion of 'private blogging' here.
TV: here's a quick update on my PVR box progress. I have a very extensive /etc/LOG which I should probably just publish as-is, really, rather than trying to make it legible ;)
Anyway, the hardware arrived last month, but the main VIA EPIA ME6000 board was non-functional -- it could never get as far as powering up the CRT for the BIOS self-test. So it was RMA'd back to http://www.mini-box.com, and they sent out a replacement, which arrived a couple of weeks ago.
I finally got to checking this out the weekend before last, and hey presto, it powered up nicely. There followed a whole week of busy nights doing a load of cautious hardware hooking-up, not-so-cautious KnoppMyth installation, and thoroughly non-cautious hacking crazily at the desired enclosure with a hacksaw (because I was too cheap to buy a Dremel).
Things got a little hairy with respect to CPU temperatures, but some looking at specs (the VIA Eden CPU can deal with up to 90 degrees C!), and repurposing of a bin-bound case fan together with some soldering and snipping, has that under control.
Eventually, we're now at the stage where it can:
and it looks good doing it, too. Credit goes to the MythTV guys for a fantastic job on their project, especially with its well-polished UI.
In addition, I have to plug KnoppMyth heavily. They're dealing with an awful situation with hardware compatibility where bleeding edge features like MPEG2 decoding and TV out are concerned, and doing a great job -- there's been several occasions where I've been staring down the barrel of a daunting patch/rebuild/test cycle, and then find out that KnoppMyth includes that component built-in for free.
But -- on the other hand -- no credit to the hardware vendors. As I link-blogged yesterday, VIA is doing the classic 'throw it over the wall' trick with respect to their linux support -- video drivers are written and deposited on their website, with scant documentation and virtually no support.
That's bad enough, but even worse is the situation with Hauppauge's PVR-250 and PVR-350 TV encoder/decoder cards. I realised soon into the setup process that other options for these should have been considered -- Hauppauge have done a great job at confusing the issue for driver developers, as far as I can see. Here's an example. When you buy a 'WinTV PVR-350' card, you may get the same box with the same manuals etc., but including these bonuses under the covers:
/etc/modules.conf for;
It's absurd. The results are threads like this and a truly daunting setup procedure, which (of course) everyone blames on the software (and Linux itself).
Anyway -- how am I doing vs. Brendan's progress? ;)
More on the latter when I eventually solve it. (it's tricky. I suspect I'll need to run two X servers with two TV-Outs to do this acceptably, and that's uncharted waters.)
Malware: spotted on NANOG -- Six PCs caused BigPond problems:
Disconnecting six compromised personal computers on Tuesday evening eased the difficulties caused by bogus requests which clogged BigPond's domain name servers (DNS), slowing customer e-mail and Web site access, Telstra said.
A Telstra spokesperson said the carrier had narrowed the list of malware that could have infected the computers to three, adding the problem could have been caused by a combination of those viruses or Trojans. He declined to name the suspects.
He said the PCs generated 95 percent of the bogus requests which caused the problems that evening.
The 'problems' in question are described here :
One forum participant (on Aussie forum Whirlpool), who claimed to be a BigPond customer, said on Monday: 'I'm in Canberra and it's been almost unusable all afternoon. I'm snowed under at the moment and it is really driving me crazy. Three out of four links fail to load first time and sometimes take eight or nine tries before it does.'
Another said: 'I am having problems loading Web pages, I get the 404 error. I have to retry five to 10 times to get some places.'
Petri Helenius, in a post to NANOG, notes:
Consumer ISP's who don't proactively take care of security/abuse usually end up with harvesting-bots which consume significant amount of DNS resources, typically doing anything from a few dozen to a thousand queries a second. A few hundred of these will seriously hamper an usually provisioned recursive server.
Interesting. It's been a long time since I've relied on an ISP's recursive DNS servers; in my recent experience (Comcast, Cox.net) they've always been overloaded, and take aaaages to give me answers. Maybe this is why.
It makes sense; most Windows machines will indeed use the ISP's NSes, because that's what DHCP tells you to do; and setting up a BIND or djbdns instance locally to query the roots directly is still a UNIX-only trick, as far as I know.
The upshot?
(PS: top tip -- ever wanted a publically-queriable recursive nameserver,
or a good IP address for pinging, that's easy to remember? 4.2.2.1
is what you're after.)
Spam: Matthew Wilson at Boomer Consulting has been having a field day -- it looks like some smart google hacking has thrown up some doozies of places that should have fixed this by now:
and my favourites:
Of course, all of these are immaterial to SpamAssassin -- we catch spammers using them anyway. But still, a surprising number of these out there.
The firm was told to pick an influenza A sample and chose from its stockpile the deadly 1957 H2N2 strain.
Check out how it was spotted:
On March 26, National Microbial Laboratory Canada detected the 1957 pandemic strain in a sample not connected with the test kit. After informing WHO and the CDC of the strange finding, the lab investigated. It informed the U.N. health agency on Friday that it had traced the virus to the test kit.
My emphasis. omgwtfbbq!
(WHO's influenza chief) Klaus Stohr said the test kits are not the only supplies of the 1957 pandemic strain sitting in laboratories around the world. 'The world really has to think what routine labs should be doing with these samples they have kept in the back of their fridges,' Stohr said.
True: the lovely C has a story from her TCD days of a vial of smallpox
found buried deep in the ice in the back of a long-forgotten freezer,
apparently rediscovered by someone during a routine spring cleaning. This
was in the early '90s, when smallpox was supposedly down to samples in
just two high-security labs, in Russia and America.
Open Source: on the 18th March the Irish Times published a commercial supplement for Microsoft. Naturally, given that it was paid advertising, there were lots of MS plugs -- but in the mix there was also a couple of more worrying articles: one by Tom Kitt, government 'Minister for the Information Society', noting
Microsoft has been one of the most innovative companies in the world and has a long track record over several decades of creating new product markets. The EU has to be open to allowing such innovation in Europe. Ireland will continue to argue at EU level, based on the solid evidence of our successful economy, that the Community must look at its rules on innovation and intellectual property rights to ensure they encourage risk taking in Europe and growth in the IT industry in the EU and around the globe.
And another with Cathal Friel, credited as 'chairman of the Irish Software Association'. Quoting the article text:
(Friel) also noted that Open Source software - which is developed by large communities of programmers and distributed for free or at low cost - is also going to have an effect on the software market. While Friel believes Open Source itself has a limited business model - 'at the end of the day, there's nothing but services to sell' - it is nonetheless becoming more pervasive and is 'a fact of life' for more traditional software companies. He believes the Open Source movement is actually stifling innovation, because fewer programmers will develop software without the financial incentive of success.
MS observers will note that both Kitt and Friel's statements mirror the MS 'party line' -- either the lads were well-briefed, or they just put their names to a story written by MS PR.
Well, there's been an interesting follow-up. Éibhear Ó hAnluain put pen to paper about Cathal Friel's statements, and received an interesting reply:
I received a 'phone call from Kathryn Raleigh, Director of the ISA, in reponse to my letter. As I was unable to take notes at the time, what follows is a memory of the conversation. She told me that the ISA would like to apologise to me for any offense that I took from the comments. She said that the first the ISA heard of the comments was after the piece was published and the Mr. Friel was not speaking with the ISA's authority. She told me that the ISA had indeed conducted some sort of analysis of the market regarding licensing and the 'proprietary' versus Free Software competition, and that the ISA's position on the matter is not to have a position. She gave me the impression that Mr. Friel has been told that he was out of line. She asked me to convey the ISA's regrets to my colleagues.
Well now, that's interesting!
I find it very encouraging to see that the ISA don't take the position noted in Friel's article, anyway. In my opinion, this is wise -- alienating free software and open-source-using companies doesn't seem likely to be a good idea, given that many of today's SMEs use open source extensively 'behind the scenes' in production, if not directly in the products they sell.
There's also the matter of Google's recent major entry into the Irish software industry, with its new offices in Barrow St. in Dublin. MS are no longer the only major multinational player on the Irish scene to whom open source's success, or failure, is a key factor in their business plans. Google use free software extremely extensively internally, are members of several major free software bodies including the FSF, and have released quite a few interesting pieces of open source software themselves.
Health: On a lighter note, I've been getting through my last two weeks mail and RSS data, and came across this beauty.
It's a truly venerable internet urban legend -- the Nepalese Nose Leech story. Even given that I assumed it was more than likely a UL, I still took care not to drink from streams when I visited leech-infested areas, especially in Nepal!
Well, it appears it may not be a UL after all --
Doctors have removed a leech from the nose of a 55-year-old Hong Kong woman after she swam and washed her face in a stream, a medical journal reported.
The woman went to her doctor complaining of nose bleeds and an occasional sensation that something was blocking her left nostril, the Hong Kong Medical Journal said in its April issue. Her family doctor noticed a brownish mass in her nostril but couldn't remove it because of heavy bleeding, the journal said.
The patient was taken to the emergency room, where doctors identified the problem as a bloodsucking leech. They had trouble pulling it out because the 2 inch invertebrate retracted into the nostril and disappeared, the journal said.
Part of the slimy leech was in a passage of her nasal cavity and a larger segment was in her sinus cavity, the article said.
Doctors used a nasal spray to anesthetize the dark brown leech that had a sucker on the front part of its body. After two minutes, the leech moved slowly out of the antrum (sinus) and was retrieved with forceps, the journal said.
The woman said that one month before her symptoms developed, she swam and washed her face in a stream while hiking. Doctors checked other members of her hiking group and found another leech in the nose of a man who washed his face in the stream, the journal said.
Link via jwz, AP wire story, abstract at Hong Kong Medical Journal site, MEDLINE abstract, including a line noting 'this form of leech infestation has not been previously reported' -- except on teh internets!
Life: Alec Muffett quotes an Economist opening line:
We tend to meet any new situation in life by reorganising, Petronius Arbiter, a 1st-century Roman satirist, is supposed to have remarked. And what a wonderful method it can be for creating the illusion of progress while producing confusion, inefficiency and demoralisation.
As apt today as it was then.
(I was recently talking to a mate who's a post-grad in the classics. She noted that classicists aren't the fastest-moving academicians around, speculating that maybe it was because, in studying the classics, you realise the same problems and the same solutions have been around for over two thousand years regardless of change in other aspects of life.)
Security: Hey user auth systems! If you're going to require me to sign in, and publish my login as a signature to prove that I'm 'me', please do me a favour -- don't delete the account if it's been 'inactive', and allow anyone to re-register that name without my knowledge!
I just tried to leave a comment on a Blogger.com weblog, to find that my user account at Blogger had been deleted. Re-creating a new account with the same name wasn't a problem -- the previous account data had been simply deleted outright. (Presumably they don't do this to people with a Blogger.com weblog -- I hope.)
The risks of this are pretty clear; given that I'd already established an identity (at least in comments on certain Blogger weblogs) as 'justinmason23', if an attacker were to have re-registered that identity before I did, they could impersonate me.
Mapping: NASA's Earth Observatory has put up a 4 MB high-res topographical image of Ireland. A rough calculation indicates that each pixel is under 0.1 of a mile on a side. It's fantastic. ;)
Best of all, since NASA operate under the US' enlightened copyright and licensing policies for government-funded data, it's free -- the masthead notes 'Any and all materials published on the Earth Observatory are freely available for re-publication or re-use, except where copyright is indicated. We ask that NASA's Earth Observatory be given credit for its original materials.' Copyright is not indicated on this image as far as I can see. So go ahead and save a copy for future use, too.
(via EirePreneur in turn via Irish Typepad)
Web: I've been doing a little thinking about group-based networking and services.
Here's the situation. Let's say you have a small group of people, and want to offer some kind of online service to them (like a private chat area, mailing list, etc. etc.) That's all well and good, but maintainance of 'who's in the group' is hard. You need:
The traditional approach is to code all that up myself, in my copious free time presumably. Urgh, talk about wheel reinvention on a massive scale.
I'd prefer to use something like TypeKey, a web service that exposes an API I can use to offload all this hard work to. Initially, I was in the 'ugh, Typekey 0wnz my auth data' camp, but I've eventually realised that (a) they're not quite as evil as MS, (b) they're not quite as stupid as MS (deleting Passport accounts if you don't log in to Hotmail, which is only one of the supposedly many services, including third party services? hello?!), and (c) it's actually really convenient having a single-sign-on for weblog commenting after all.
Having said all that -- TypeKey's out. Unfortunately, it only does authentication, without dealing with group maintainance.
However, social networking services are all about groups and group maintainance.
Running through the options -- LinkedIn, Friendster and Orkut are all grabby and gropy and 'my data! mine!', so they're out immediately.
The next step was to take a look at Tribe.net, which seems kind of nice and had a good rep for open APIs -- but as far as I can see, all they've got really in that department is FOAF output, and a simple server-side-include thing called TribeCast. I could list all the group members in a FOAF file, but without authentication, that's pretty useless since anyone could claim to be one of the FOAFs.
That leaves Flickr, which has a great set of APIs. Using that is looking quite promising. If you're curious, I've gone into detail on this at the taint.org wiki.
Patents: DCC (Distributed Checksum Clearinghouse) is a venerable, and widely-used anti-spam system created by Vernon Schryver; we've supported it in SpamAssassin for yonks.
It now appears that DCC is now no longer open source software; it's still free for personal and noncommercial use, but this clause has been added to the new license text:
This agreement is not applicable to any entity which sells anti-spam solutions to others or provides an anti-spam solution as part of a security solution sold to other entities, or to a private network which employes DCC or uses data provided by operation of DCC but does not provide corresponding data to other users.
So there's talk that those commercial users should now license it -- interestingly, from another company called Commtouch, not Vernon's Rhyolite Software. (More info).
It appears that the license change is part of an agreement with Commtouch, owner of US Patent 6,330,590, a patent on the idea of hash-sharing antispam techniques. (I haven't read the patent due to ASF and other policies so I can't tell you what it really covers.)
It looks like we'll be disabling DCC's use in SpamAssassin by default, as we did with Razor, as a result. (Our policy is that the default ruleset used in SpamAssassin be usable by anyone who can use our software, so that the normal usage is open source by default, rather than subsets of the overall functionality.)
Web: Now this is very cool stuff: 'Greasemonkey is a Firefox extension which lets you to add bits of DHTML ("user scripts") to any webpage to change it's behavior.'
In other words, you can rewrite any page viewed in Firefox, as it transits between the server and your client's display; a form of transcoding.
Traditionally, transcoding is performed using a HTTP proxy which applies the transformation, or a specialised HTTP user agent which transcodes and outputs a whole new set of documents with the results.
That was all a little hacky for full-scale integration into your web browser, though, so Greasemonkey is a big improvement for that use-case.
Some good links:
And some demos:
Remember, these are single, sub-100-line JS scripts, running entirely locally in the user's web browser. The last one gives you an idea of what coolness is possible...
My contribution: an ad-removal script for Metafilter. It took some 30 seconds of hacking to produce this -- soooo easy. It's a whole new world of site customisation and hackable filtering. You thought AdBlock was good, this is ever niftier ;)
Tax: Following on from the previous entry, I've had a stroke of luck. It turns out that I did indeed quality as a US resident for tax purposes, and therefore could use Turbotax.
20 minutes later, both state and federal forms were e-filed with the very minimum of fuss -- computers and the net illustrating their worth as labour-saving devices quite nicely. ;)
(Oh -- also -- a PSA for Google's benefit: I'm pretty sure that form 6251 had incorrect instructions. It claims that the items it refers to in form 1040, can also be referred to in form 1040NR by the same numbers. In fact, parts of 1040NR are radically different in numbering than 1040. It's a bug in the form!)
Taxes: it's that time of year again, when every inhabitant of the US, resident and 'non-resident', gets The Fear. Yep, it's tax time. (Warning: this is a long and protracted vent.)
In the US, every worker is required to prepare and file their own taxes, in detail. Nowhere outside of India can do bureaucracy quite like the US, as far as I can tell -- even the brits have embraced simplicity to a greater degree -- so this is no trivial undertaking; however, they do have a few outs, if you're eligible.
Naturally, given my luck, I'm not. ;)
Now, I'm no slouch when it comes to form-filling; I've had to deal with messy forms many times before. But these are masterpieces. Check out this gem:
The ATNOLD is the sum of the alternative tax net operating loss (ATNOL) carryovers and carrybacks to the tax year, subject to the limitation explained below. Figure your ATNOLD as follows.
Your ATNOL for a loss year is the excess of the deductions allowed for figuring AMTI (excluding the ATNOLD) over the income included in AMTI. Figure this excess with the modifications in section 172(d), taking into account the adjustments in sections 56 and 58 and preferences in section 57 (that is, the section 172(d) modifications must be separately figured for the ATNOL). For example, the limitation of nonbusiness deductions to the amount of nonbusiness income must be separately figured for the ATNOL, using only nonbusiness income and deductions that are included in AMTI.
Your ATNOLD may be limited. To figure the ATNOLD limitation, you must first figure your AMTI without regard to the ATNOLD. To do this, first figure a tentative amount for line 9 by treating line 27 as if it were zero. Next, figure a tentative total of lines 1 through 26 using the tentative line 9 amount and treating line 27 as if it were zero. Your ATNOLD limitation is 90% of this tentative total.
Enter on line 27 the smaller of the ATNOLD or the ATNOLD limitation.
Any ATNOL not used may be carried back 2 years or forward up to 20 years (15 years for loss years beginning before 1998). In some cases, the carryback period is longer than 2 years; see section 172(b) for details. The treatment of ATNOLs does not affect your regular tax NOL.
That pretty much appears as-is; there's no additional explanation of those acronyms elsewhere, it's just a big block of jargon. Obviously not intended for human consumption. There's also this:
Medical and Dental. Enter the smaller of Schedule A (Form 1040), line 4, or 2.5 % of Form 1040, line 37.
That seems well and good, and according to the instructions, the 1040NR is 100% compatible with the 1040. Except Schedule (Form 1040NR), line 4 is:
Gifts to U.S. Charities. Gifts by cash or check.
What do charity donations have to do with medical and dental expenses? WTF? (I suspect the compatibility claim is incorrect.)
Last year, I hit up H&R Block for their help; it saved a lot of hassle, but was pretty expensive, costing over $200. Overblown TV advertising alert: of course there was no great refund, despite what their ads claim. However they did recommend that I donate old clothes to thrift stores, keep the receipts, and claim that back as a tax contribution. I'm serious. Given my wardrobe, that should net about $10.
This year should be a lot simpler, since I'm just a US nonresident working visa holder doing nothing but paying plain old income tax -- so I was intending to just fill out the forms myself.
I think I'll tick that idea off my list and check out the online options.
All I can say is, no wonder quite a few US citizens seem to think that government involvement is something to be minimized if at all possible. There are alternatives though -- I'd happily take an Ireland-style 'nanny state' which will compute my tax liabilities for me if I so choose. It's not like I'd be in a position to argue with them anyway, aside from the common case of hiring a tax attorney, if we disagree; so why not let the government do the heavy lifting? ;)
(PS: the good news is it now appears I may qualify as a resident. This means Turbotax.com is a viable option... yay!)
Misc: So I was travelling last week -- a very productive trip to the UK visiting the main work dev office, and getting a little socialising in too while I was at it. A pretty good trip overall, especially since I seem to have figured out how to use my frequent flyer miles effectively to get great seats! ;)
Here's a good interview with SpamAssassin PMC chair, Daniel; well worth a read if you want to see what we in SpamAssassin think about the state of the onion in spam-filtering.
In not-so-good news, it seems Charlie McCreevy has managed to push the software patent directive through, despite massive EU Parliament unhappiness. Third time around at the Fisheries meeting, naturally; and there's some serious questions about the legitimacy of the procedural rules invoked by the Commission in refusing to take the directive off the A-item menu. Now that's what I call democracy...
It can still be defeated, but it's an uphill battle now -- for it to be thrown out in the second reading at the European Parliament, it'll need a two-thirds majority of all MEPs (not just the MEPs present), reportedly.
In the meantime, thanks to the FF and PDs' bullying tactics, Ireland's small but growing pool of homegrown software developers are being ignored, and the Irish software industry looks more like a lame import operation for the likes of Microsoft. Our reputation is dragged through the mud for a few multinationals, and the rest of Europe resents us for it. Wonderful.
BTW, even if it does pass, there are ways to fix it -- directives must be implemented into national law in each country. This means that Ireland could still write their implementation of the directive to exclude software inventions (even the ones where it's supposedly a patent on hardware like 'a CPU connected to a hard disk, with such-and-such software running on the CPU'). However, given McCreevy's obvious bias in favour of getting this specific text into place, how likely is that going to be?
Patents: So the Conference of Presidents has ratified the JURI decision to throw out the flawed software patents directive text. Phew! That's a lot more pressure on the European Commission. Charlie McCreevy could still carry on his attempt to steamroller European democracy on this one, but it looks likely that he wouldn't get away with it now -- possibly facing sanctions as a result.
Found in a Slashdot comment -- an amazing quote from Michel Rocard (former French Prime Minister, now European Deputy), recounting a meeting with Microsoft representatives on the software-patent issue:
"We never could (speak) a common language with the companies representatives we met - in particular those from Microsoft. Speaking about (the free circulation of ideas), free access to knowledge, was like speaking chinese to them. In their way of thinking, everything that is not usable for immediate profit ceases to be an engine of growth. They don't seem to be able to understand that an invention which is a pure spirit creation (sic) can't be patented. It's simply terrifying. Many of us, at the Parliament, agree to say that they never have know such a pressure and such a verbal violence during their parliamentary work. It is a huge case."
In addition, he takes aim at the Irish Presidency's tactics:
"To adopt it formally, there is an expeditious procedure -- the (A-item) at the Council of Ministers, where the it is adopted without discussion. The Irish and Dutch presidencies attempted this tactic three times, twice at meetings of the (Fisheries Council)! This is simply scandalous."
Blimey, he's really pissed off. Great! Go Rocard! ;)
See here for the original interview (in French), and here for a bad Babelfish translation.
In happier news -- take a look at some pictures from the presentation of 30,000 verified signatures (and flowers!) from people around the world, thanking the Polish Government for their repeated stands against the flawed directive in December.
Code: Ugo Cei: Building Interactive Web Programs with Continuations quoting Phil Windley:
This leads to the question: what if I could write programs for the Web that were 'structured' in the programming sense of that word? The result would be Web programs that were more natural to write and easy to read. You'd no longer have to maintain the state of your program outside the language and the data could be kept in variables, where it belongs. The answer is: you can.
I hate the 'save all state' model imposed by developing for the web, and have been hoping for a way to do this for a while -- and now I know what it's called ;)
It seems Seaside is the leading continuations-based web-app framework, using Smalltalk, and (as Ugo noted) Apache Cocoon has it too, but there's a whole load more. Can you tell I haven't been following web-app development techniques much recently?
Never mind those other languages, though -- Continuity looks promising as a Perl framework based around continuations. Perl 6 will reportedly have native continuation support, and Dan Sugalski gives a good write-up of how they're implemented and their ramifications there.
Patents: Børsen: Bill Gates threatened to kill 800 Danish jobs if Denmark opposed software patent directive:
Danish financial newspaper Børsen reports that Microsoft founder Bill Gates threatened the Danish government in connection with software patents. According to the article, Gates told Rasmussen and two Danish ministers in November that he would kill all 800 jobs in Navision, a Danish company acquired by Microsoft in 2002, unless the EU were to quickly decide to legalize software patents through a directive. Denmark is a country with only 5 million inhabitants and a relatively small high-tech sector to which the loss of 800 jobs would have significant implications.
Lovely -- a blunt blackmail attempt. The article goes on:
It would not be the first threat of its kind. A group of large corporations including Philips is reported to have previously threatened European governments to outsource all of their European software development jobs to low-wage countries unless the EU were to allow patents on software through the directive that is currently being worked on.
In January, leading Polish daily Gazeta Wyborcza reported on a letter addressed by the Polish subsidiaries of Siemens, Nokia, Philips, Ericsson and Alcatel to Poland's prime minister Marek Belka ... it is said to have indicated that the respective companies would reconsider making investments in Poland if the Polish government upheld its resistance to the legalization of software patents in the EU.
Again, note the FUD-busting on this point. I notice that Florian Mueller of NoSoftwarePatents.comhas a a good one-liner response along the same lines -- 'The country in which you develop a technology has nothing to do with where you can take out patents.' He goes on:
If they move jobs to Asia, they won't get a single additional patent, neither in Asia nor in Europe. If you warn politicians of consequences that are directly related to a legislative issue, that's acceptable. If you threaten with causing damage that has no factual connection whatsoever, then it's blackmail. Plain and simple.
Tech: Bit of a long essay, this one.
World+dog have been linking to this interview with Flickr's Stewart Butterfield on the O'Reilly Network, so I wasn't going to bother. But I came across a great illustration of what I think is a very important point:
Koman: In the write-up for your web services session at ETech, you say, Capturing the creative energy of the hive can be scary. It requires giving up some control, and eliminating lock-in as a strategy. Tell me some more about that.
Butterfield: Ofoto is a pretty good example. I don't want to pick on them too much, but they create a pretty artificial kind of lock-in. When you upload your pictures to them, you might upload a three- or four-megapixel image, but all you can get back from them is a 600-pixel image; if you want to get the original back, you have to buy it on a CD. There's no way to get it out because if you got it out, then your friends and family could get it out and print it out at home, and they're in competition with Lexmark and HP as well as the other online photo services. So that's one aspect of it.
There's also a tendency to want to capture all the value that's being generated or will potentially be generated by new business. What I mean by that is, we don't explicitly allow commercial uses of the API yet, but we definitely plan to. And we know that there are people working on products based on our API that we want to do, but outside developers will get to it first. What letting go in that context means is letting go of all the control you have over users by being the one who owns the database, because other developers can generate businesses and products that hook into you, and that takes some value away.
This is a point that still, to this day, most people miss.
The traditional viewpoint is that, if you've got something, you hoard it, and ensure you're the guy who makes the money from it. So you do what Ofoto do -- you keep the full-resolution images, and charge for access to them; or you don't publish APIs, and keep the data to yourself; or in the world of source code, you hold onto the source so no-one else can see it, because it's your 'crown jewels'. Then, the idea goes, you can ensure that you're the only one who can do prints, or add a feature to the source, or whatever.
But the problem is, you're not always the one with the idea; or alternatively, every feature request has to go through you, and be implemented by you, on your time. And in the meantime, your users are considering the big question -- 'do I want to get locked in, here? what if he goes out of business? am I a small customer who's going to be ignored?'
In fact, I've been guilty of this myself. When I started writing open-source software, I used the GPL as a license, which prohibits commercial use (mostly) -- except by myself or through my explicit permission. I had no intentions of making it available for commercial use, because I couldn't see the commercial uses.
But that was me being short-sighted -- soon, people starting asking if they could license the code for commercial use, or hire me. I realised that I didn't have the time, or inclination, to go the whole hog, and risk my livelihood on a piece of software -- especially risky since I didn't think that software could support me alone.
So when I wrote SpamAssassin, I picked the Perl dual license, a license that did permit commercial use, while still being an open-source license. By now, there are quite a few commercial versions of SpamAssassin, all making money (I hope!), I'm getting paid to work on SpamAssassin, and everyone's happy ;)
Perhaps I should have kept commercial rights to myself. But I have no doubt that doing so would have ensured SpamAssassin remained a small-time solution, and would not have received the number of contributors, committers, and patches it has by now. (for example, Matt Sergeant, who was an SpamAssassin committer, joined the project explicitly to use that code in MessageLabs' product.)
Plus, at the time, there were already quite a few commercial competitors -- and there's a lot more to being a commercial success than the simple things required to be an open-source success; I'd be dubious that SpamAssassin would have been able to compete as a purely-commercial play, and I'm not sure I'd have been keen to risk my livelihood to do so, anyway. (I'm not really dot-com CTO material, anyway. I like hacking code too much.)
I think things have worked out well: the software's better, I'm earning a livelihood from open-source software regardless, and the software's usable for more people. As usual, Larry Wall was right ;)
Spam: recently, I've been getting a lot of spam bounces; that is, messages sent by people's autoresponders, in response to forged spam claiming to come from my domain. (I have an SPF record, but these autoresponders naturally don't bother to check that before replying.)
I have a SpamAssassin ruleset which catches these, and it gets rid of the vast majority -- but the odd wierd one gets past. This one caught my eye before I deleted it:
On October 5, 2004, I will be going to the Illinois Department of Corrections for approximately 18 months. If you wish to contact me, please snail mail me at: (address deleted)
Your letters will be forwarded to me and I will reply as soon as I receive them! Thanks...and please do write! Mail is vitally important! :-)
... ouch. Good luck to this guy, whoever he is...
Spam: Should ISPs Be Profiting From Knowingly Hosting Spam Gangs? -- a new article up on Spamhaus.org, well worth a read. Some snippets:
So where is this stealth proxy spamware sold and distributed from? For Send Safe the answer is, www.send-safe.com, hosted by MCI Worldcom.
... MCI executives have refused to stop providing service to these gangs, insisting that the sale and distribution of stealth spamming software is not against MCI's policy.
... It's no surprise therefore that MCI has consistently occupied first place in Spamhaus TOP 10 World Worst Spam Service ISPs chart, with over 200 spammers and spam gangs on the MCI network in full knowledge of the security managers and the General Counsel.
... MCI Worldcom's official position on the issue is that MCI can't stop their spam gangs selling proxy hijacking spamware from MCI's network as that would be 'censoring' the distribution and sale of illegal proxy hijacking software.
Antarctic: It seems that Ernest Shackleton, during his exploration of Antarctica, relied heavily on 'Forced March' tablets:
Reportedly 'sold over the counter at Harrod's until 1916', these were primarily cocaine-based.
Using sound as a dead man’s switch
Software: a nifty trick in this Slashdot comment:
Nowadays, I'd probably pay the money for a hardware watchdog timer. But this is a good, cheap way to implement a dead man's switch. Very clever!